- 08 Nov 2024
- 11 読む分
- 印刷する
- PDF
SSO Configurations for Linux Devices
- 更新日 08 Nov 2024
- 11 読む分
- 印刷する
- PDF
This document provides a step-by-step guide for setting up SSO Configuration to configure Google Workspace, allowing users to sign in to any Google Workspace application like GMail, Google Drive etc using their OneIdP credentials and securely access these services on Linux devices.
Pre-requisites for Linux
- Linux Device(s) should be part of User Group. A profile should be associated with Linux from the User Groups section on Scalefusion Dashboard.
- User should be assigned to Linux Device
- On the device, user account with the same name (user assigned to device) should exist.
Steps for Linux devices
Prior to creating an SSO Configuration for Linux, you need to take these steps:
Associate Device Profile with Linux in User Groups
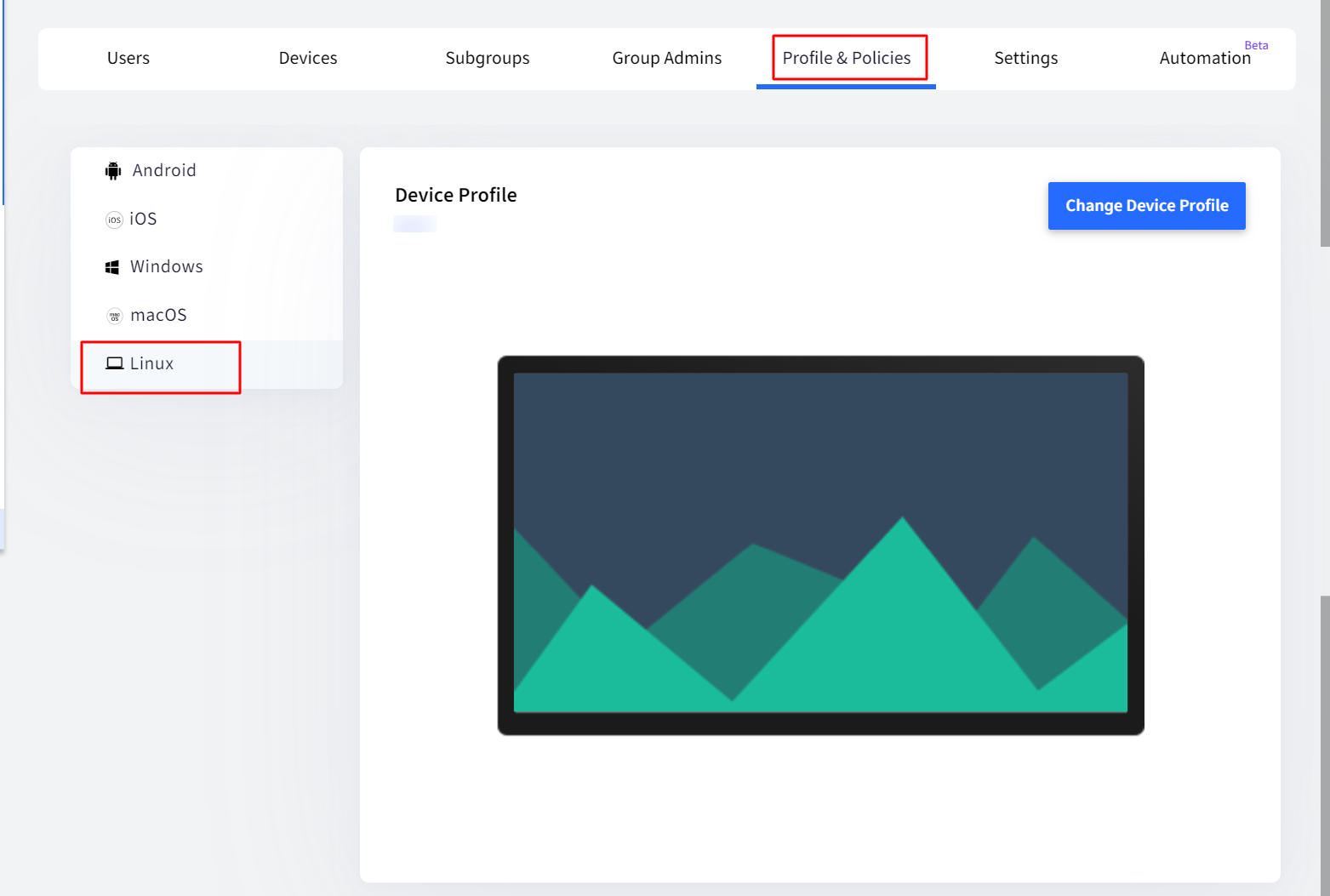
- On Scalefusion Dashboard, navigate to Groups > User Groups
- Click on View Details for the Group under which you want to associate Linux profile
- Go to Profiles & Policies and click on Linux
- Click on Change Device Profile, select the Linux Device Profile and Submit
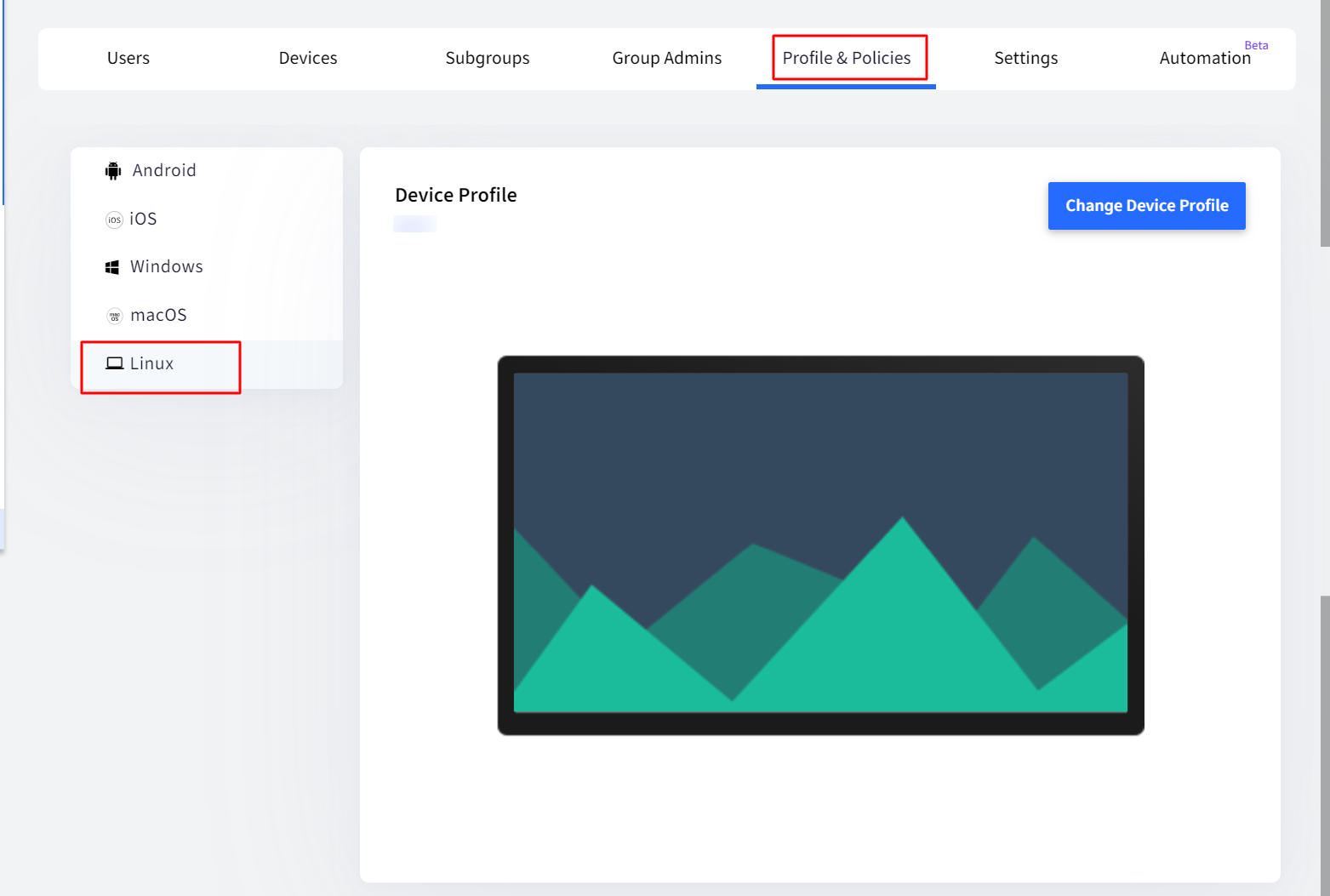
- Click on Apply
Assign User to Devices
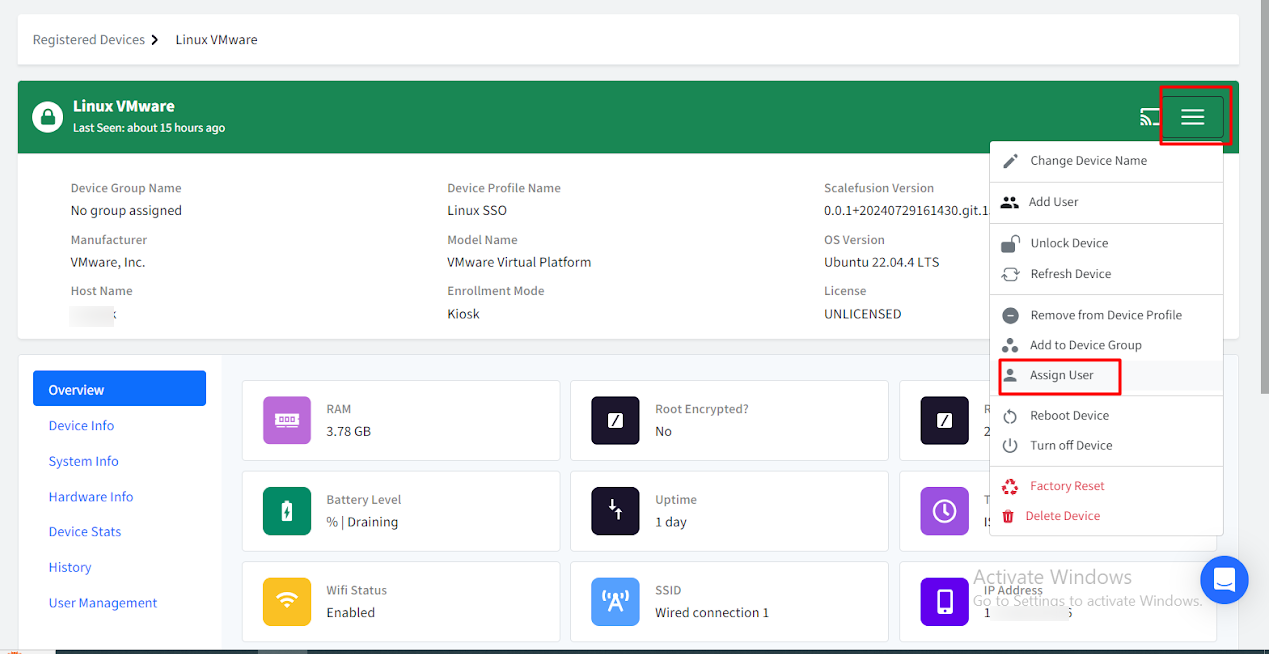
- On Scalefusion Dashboard, navigate to Devices section.
- Click on the Linux device.
- Click on the three horizontal lines on the right and select Assign User from the menu.
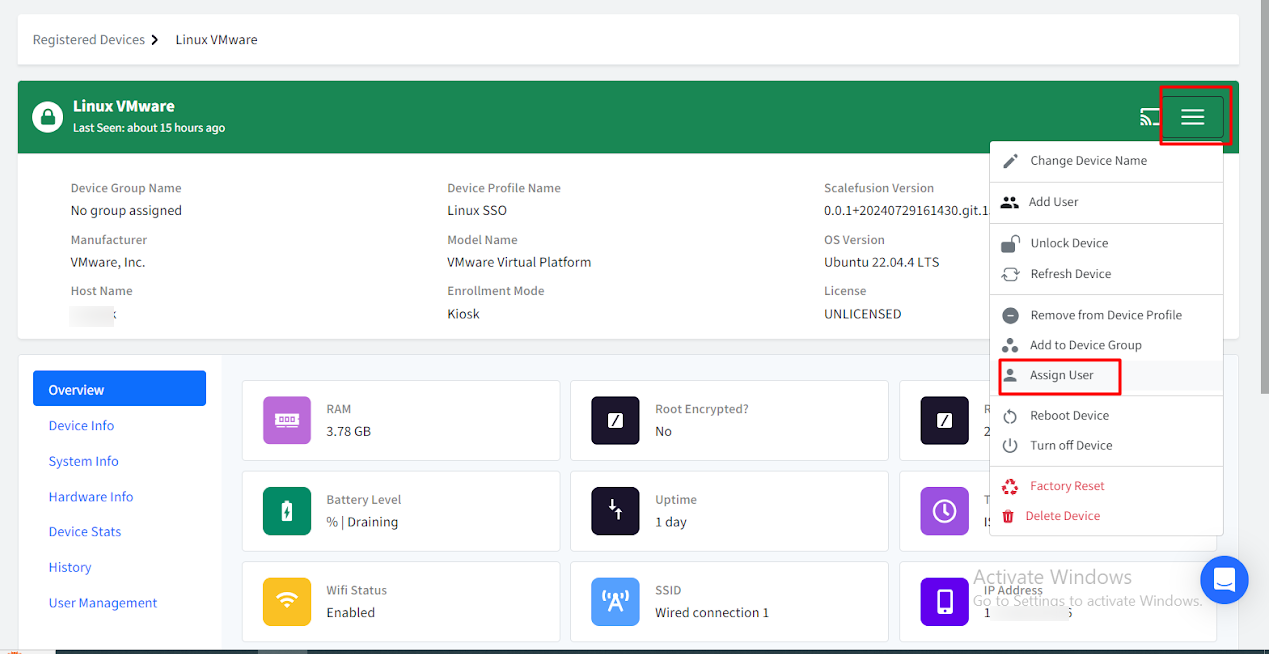
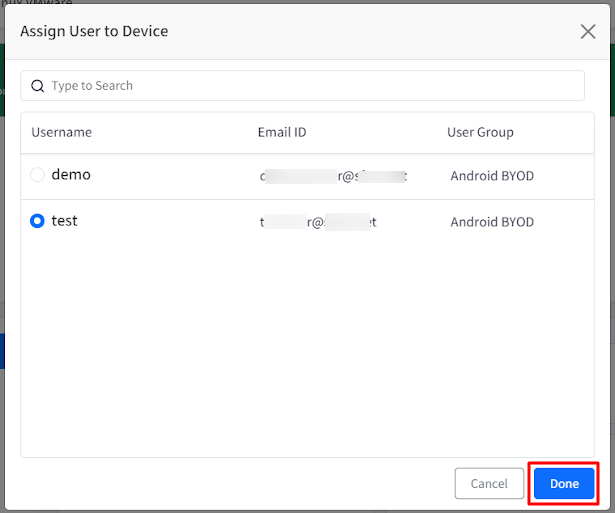
- A pop-up window Assign User to device will open.
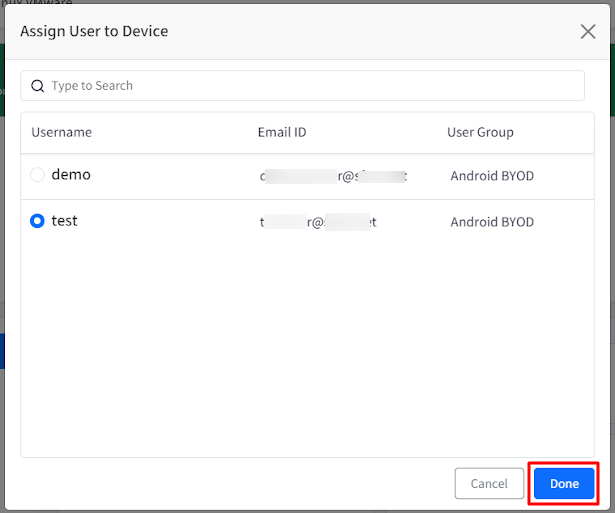
- From the list of users, select a user to be assigned to the device.Important:
- The user you are assigning, should be part of the respective User Group (added under Users)
- Please ensure a user with the same name exists on the Linux device
- Click Done
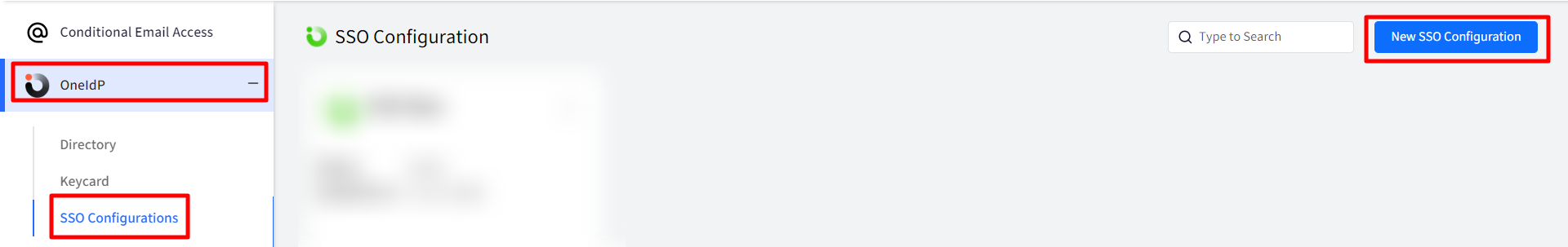
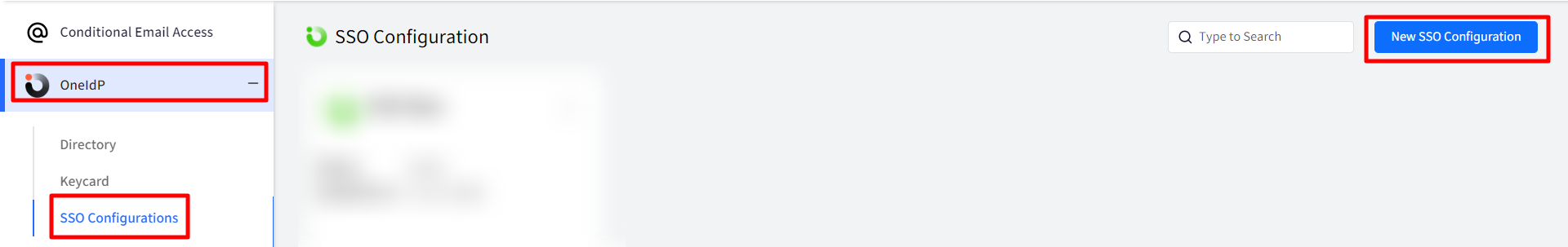
Once the above process is done, you can navigate to OneIdP > SSO Configuration to create SSO Configuration
Steps for SSO Configuration
Pre-requisites
- The devices should be enrolled with Scalefusion.
- The Custom Domain for which you are authorizing, should be verified through OneIdP.
- Users belonging to custom domain should be imported/added to Scalefusion Dashboard and migrated to OneIdP.
- IT Admins should have access to Google (Service Providers') admin console.
Steps
- Navigate to OneIdP > SSO Configuration
- Click on New SSO Configuration button on top right.
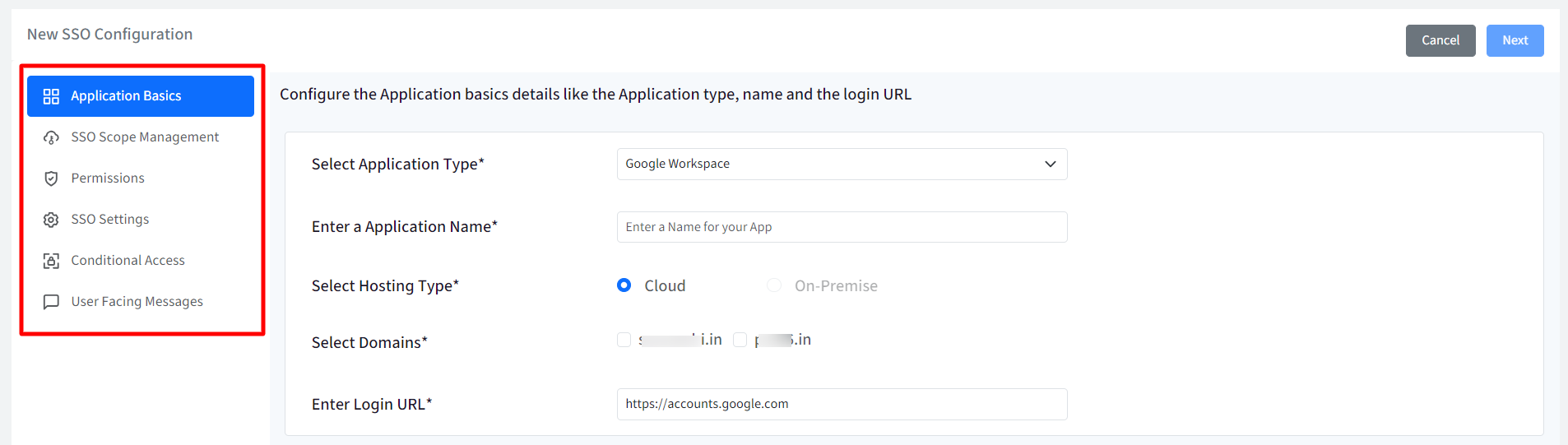
- This opens the SSO Configuration wizard with following tabs on the left panel:
- Application Basics
- SSO Scope Management
- Permissions
- SSO Settings
- Conditional Access
- User Facing Messages
Navigate to each tab and enter required details. You can navigate to next tab only after you have entered complete details in the current section. All are explained in detail below.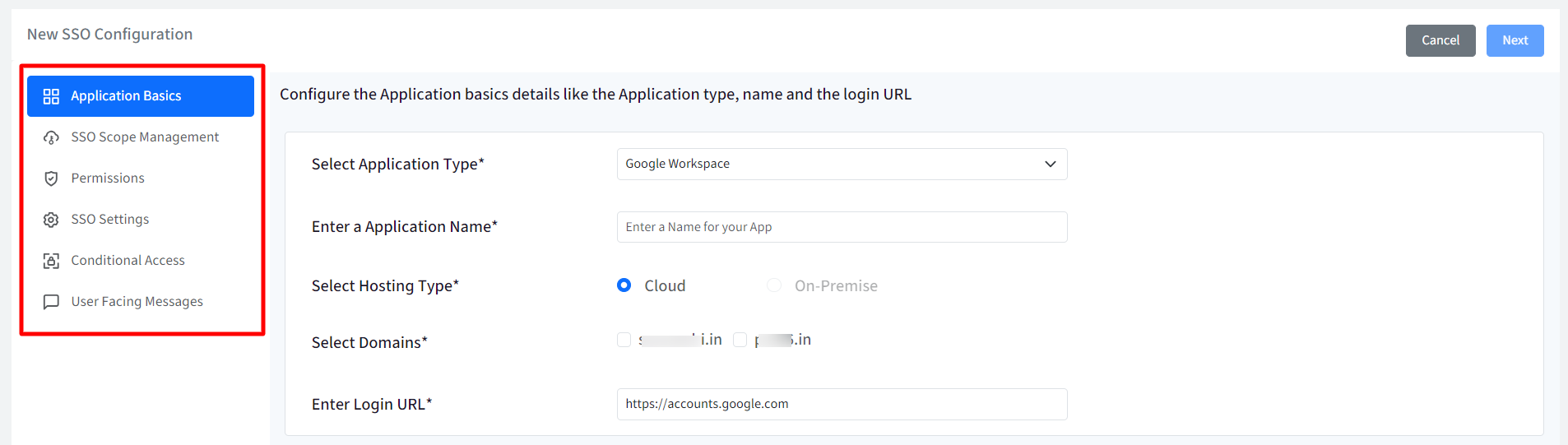
Application Basics
Configure basic application details by entering the following:
- Select Application Type: Select Google Workspace as application type from the drop-down.
- Enter Application Name: Enter a name for your App which will be an identifier for your configuration. The name must be at-least 5 characters long. The maximum allowed length is 128 characters.
- Select Hosting Type: This will be pre-selected as Cloud
- Select Domains: All the custom domains you have configured and verified using OneIdP, will be listed here. Select the domain(s) which you want to be SAML SSO enabled. You can create multiple SSO configurations with same domains.
- Enter Login URL: Provide URL that you use to sign in to that service. In case of google, it will be pre-populated as https://accounts.google.com
Once you have entered all details click Next
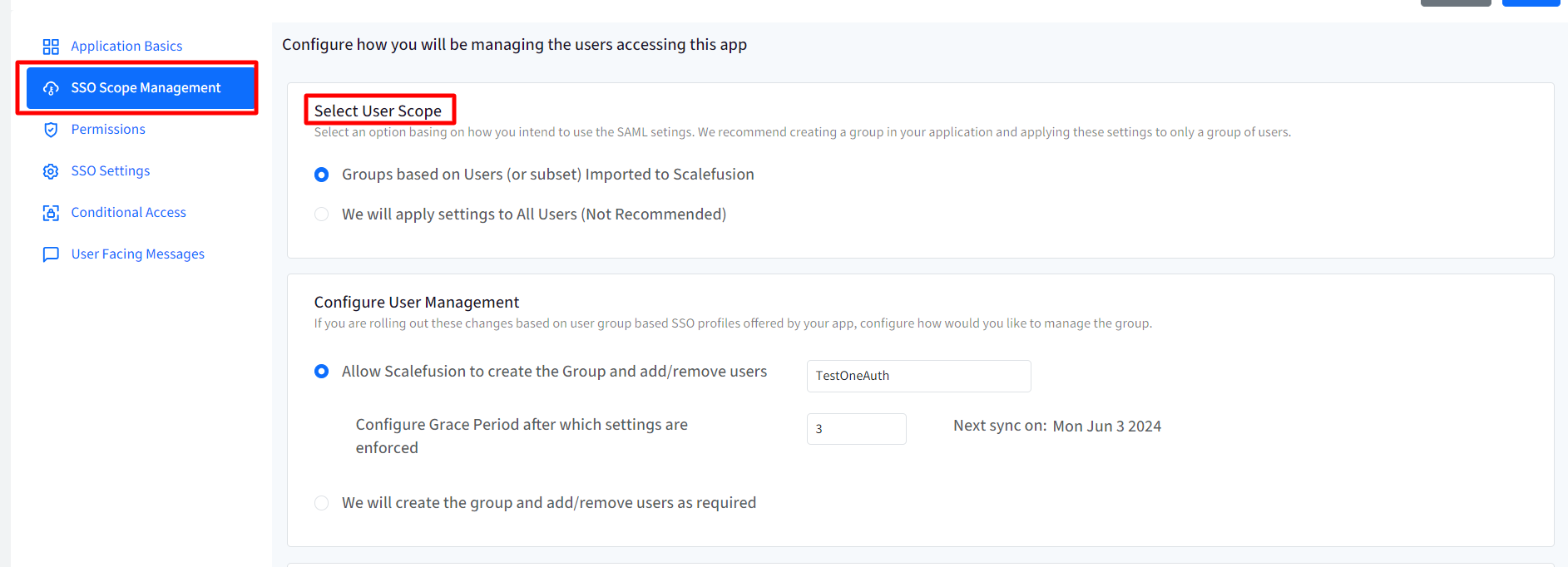
SSO Scope Management
With SSO scope management you can configure the procedure for managing the users who will be accessing this application. It basically allows how SAML settings for the users are going to be managed. Following are the settings:
Select User Scope
Select one from the following options basing on how you intend to use the SAML settings. It is recommended to create a group in your application and applying these settings to only a group of users. Select one from the following:
- Groups based on Users (or subset) Imported to Scalefusion (Default)
- We will apply settings to All Users (Not Recommended)
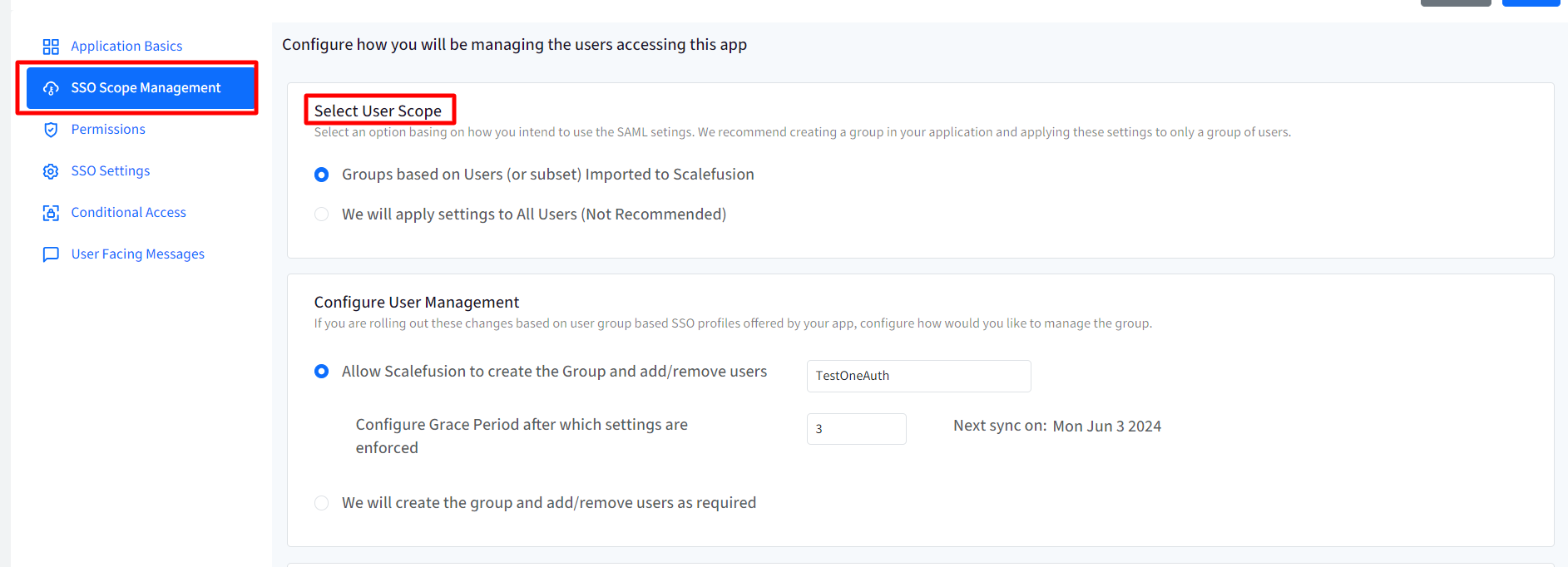
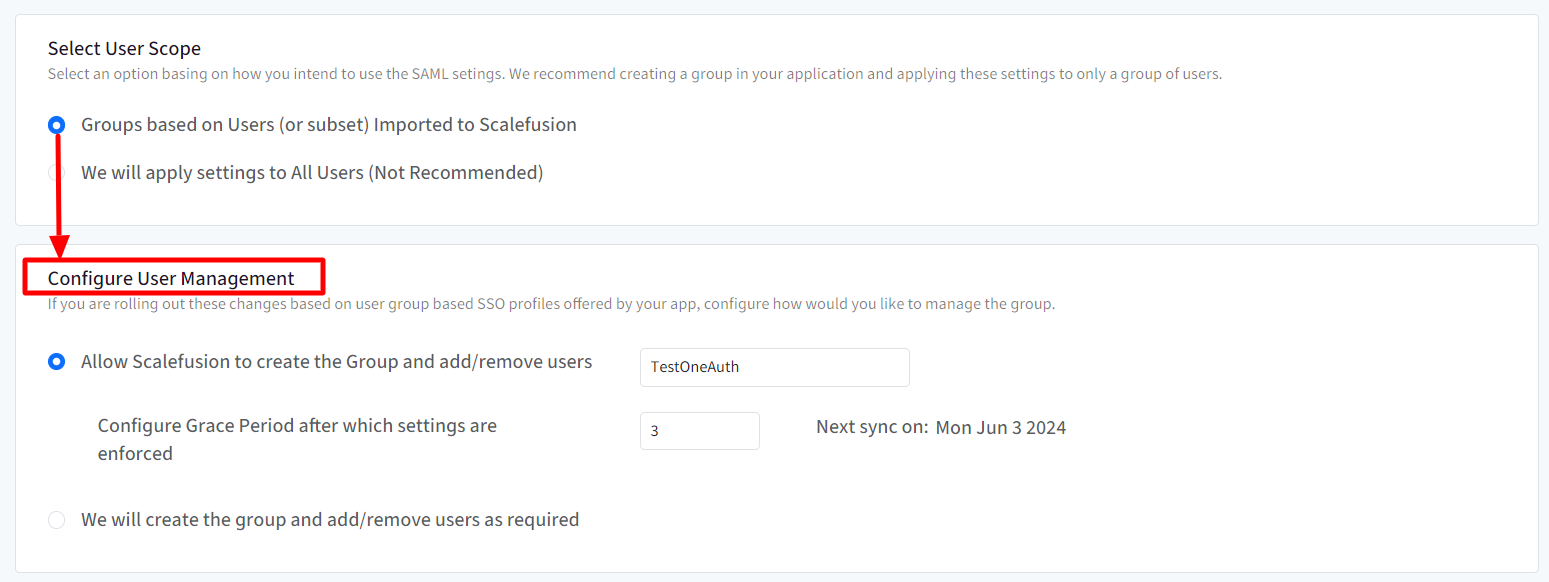
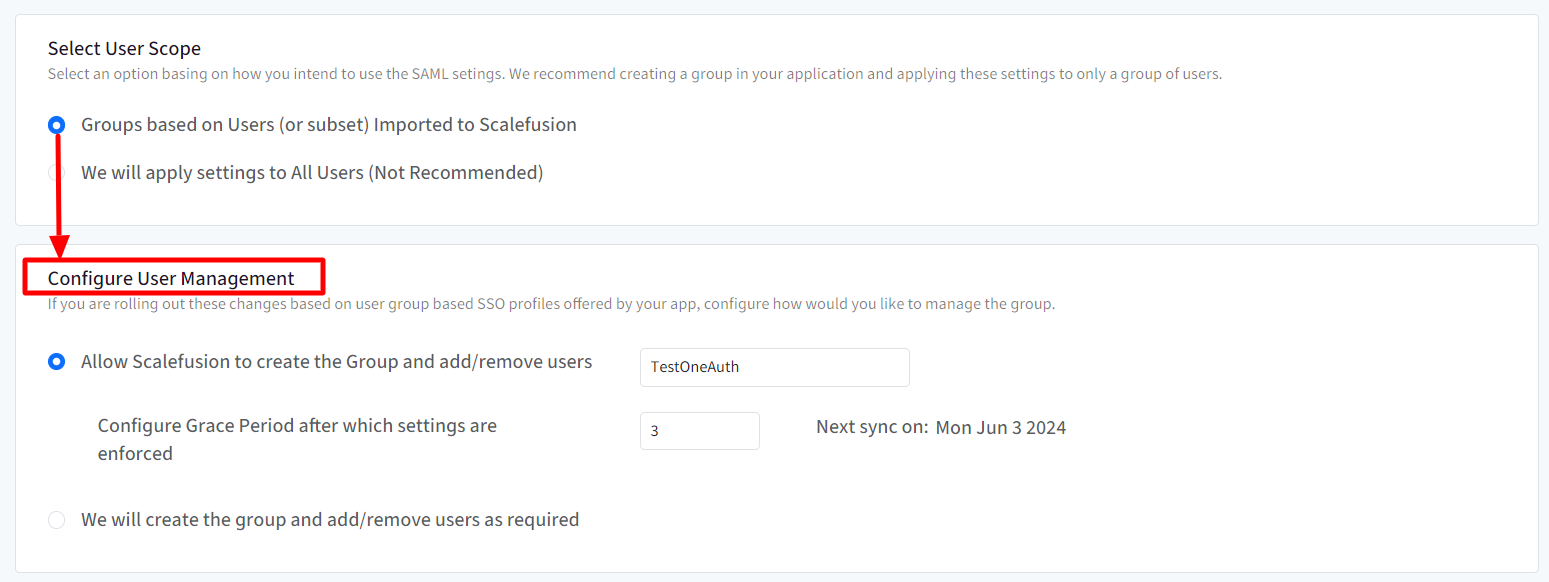
Configure User Management
If you intend to roll out the changes based on user-group based SSO profiles offered by your app, configure how would you like to manage the group. Hence, these settings will be enabled and become configurable only when groups based on users imported to Scalefusion, is selected as User scope in the setting above. Choose one from the following two options:
- Allow Scalefusion to create the Group and add/remove users:Enter the name of Group. With this, a group with the name you have mentioned, will be created on the admin console and users will be moved to that group.
- Configure Grace Period after which settings are enforced: Enter the time (in days) after which SSO Configuration settings will be enforced on users. Grace period can be anywhere from 2 to 30 days.
- We will create the group and add/remove users as required: The group can be created on the console and users can be moved to the group as per requirement.
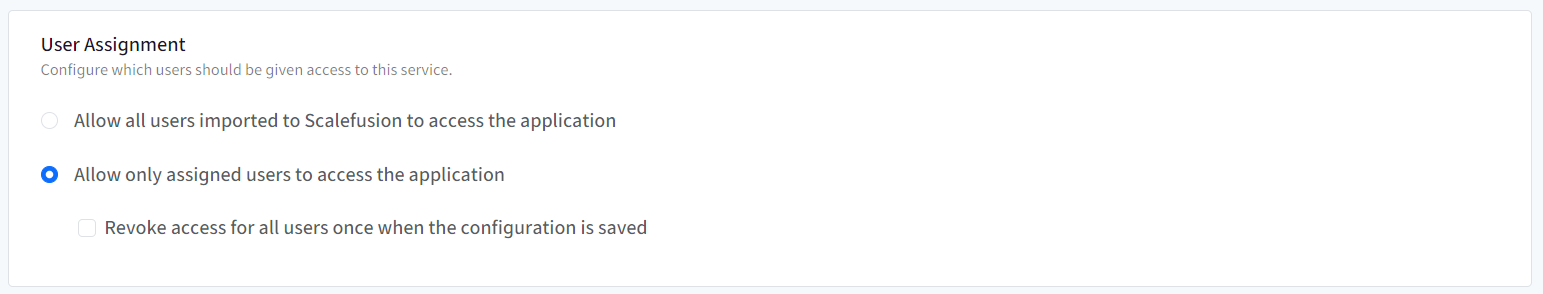
User assignment
SSO Configuration would allow only assigned users to access the app. Choose one from the following options:
- Allow all users imported to Scalefusion to access the application: All users (belonging to the domain) imported to Scalefusion will be allowed to access the application
- Allow only assigned users to access the application: Only the user(s) whom you have assigned the SSO configuration, will be allowed to access the application. With this option, after SSO configuration is created, you need to manually select and assign the users.
- Revoke access for all users once when the configuration is saved: If this is checked, the access is revoked from the users who are currently assigned with the configuration. As a result, it will invalidate all user sessions and logout users from their current running session.
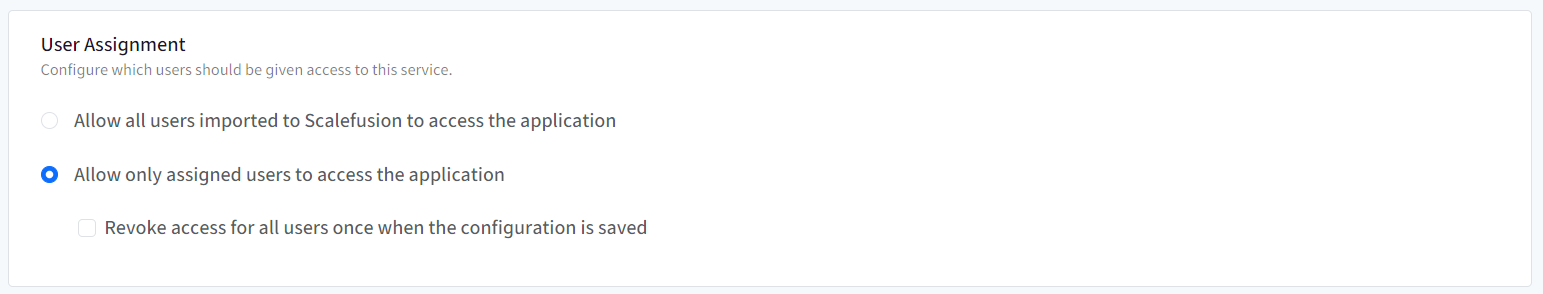
- Revoke access for all users once when the configuration is saved: If this is checked, the access is revoked from the users who are currently assigned with the configuration. As a result, it will invalidate all user sessions and logout users from their current running session.
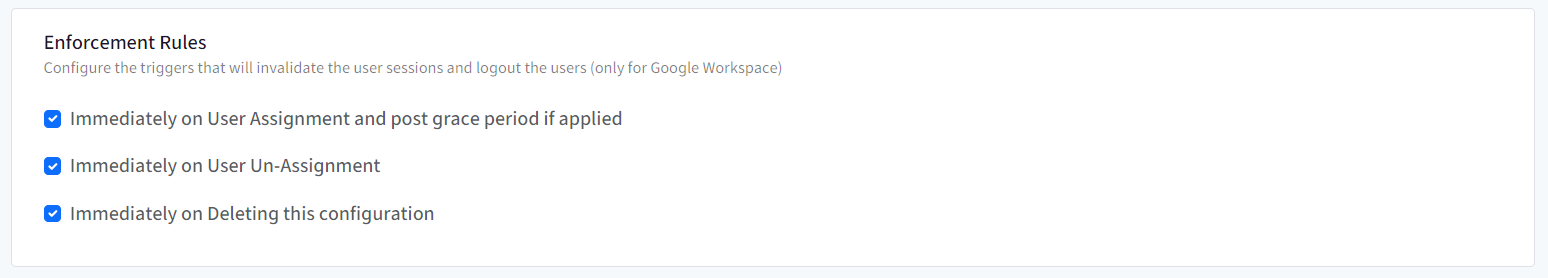
Enforcement Rules
From you can configure and enforce users that at what point of time SSO Configuration should invalidate the current session and logout users (only for Google Workspace). Following options can be selected:
- Immediately on User Assignment and post grace period if applied: When grace period is applied and user gets automatically added in the group on the admin console.
- Immediately on User Un-Assignment: When user is unassigned the SSO configuration
- Immediately on Deleting this configuration: When SSO configuration is deleted from Scalefusion Dashboard
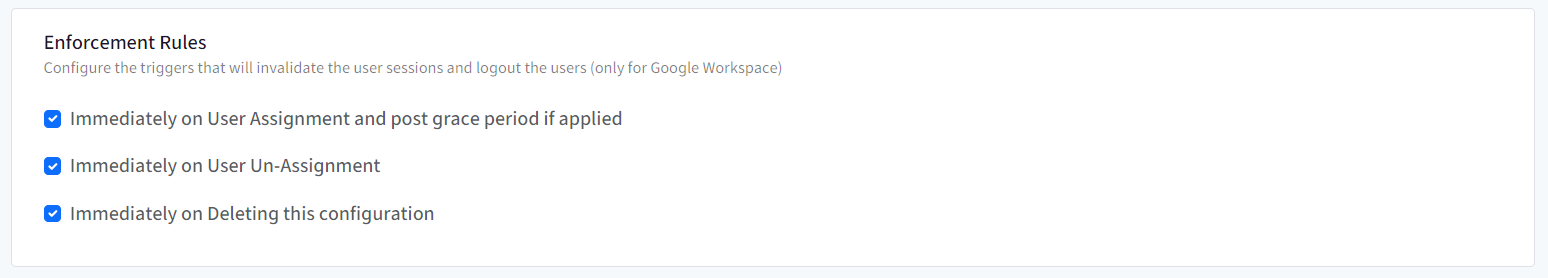
Click Next
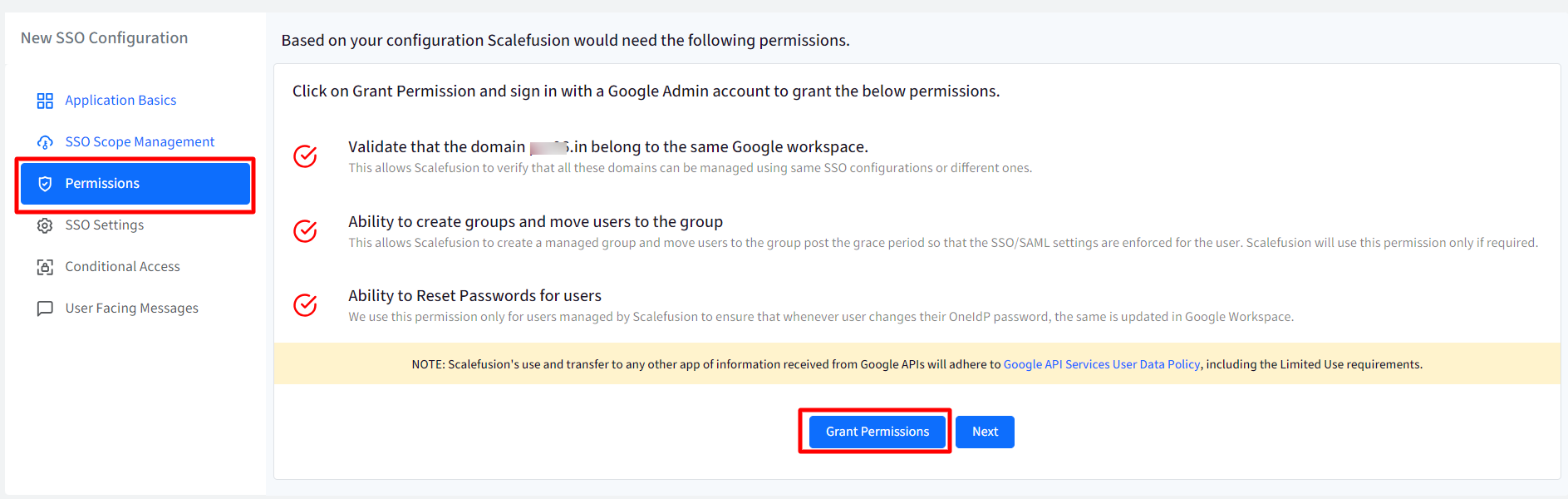
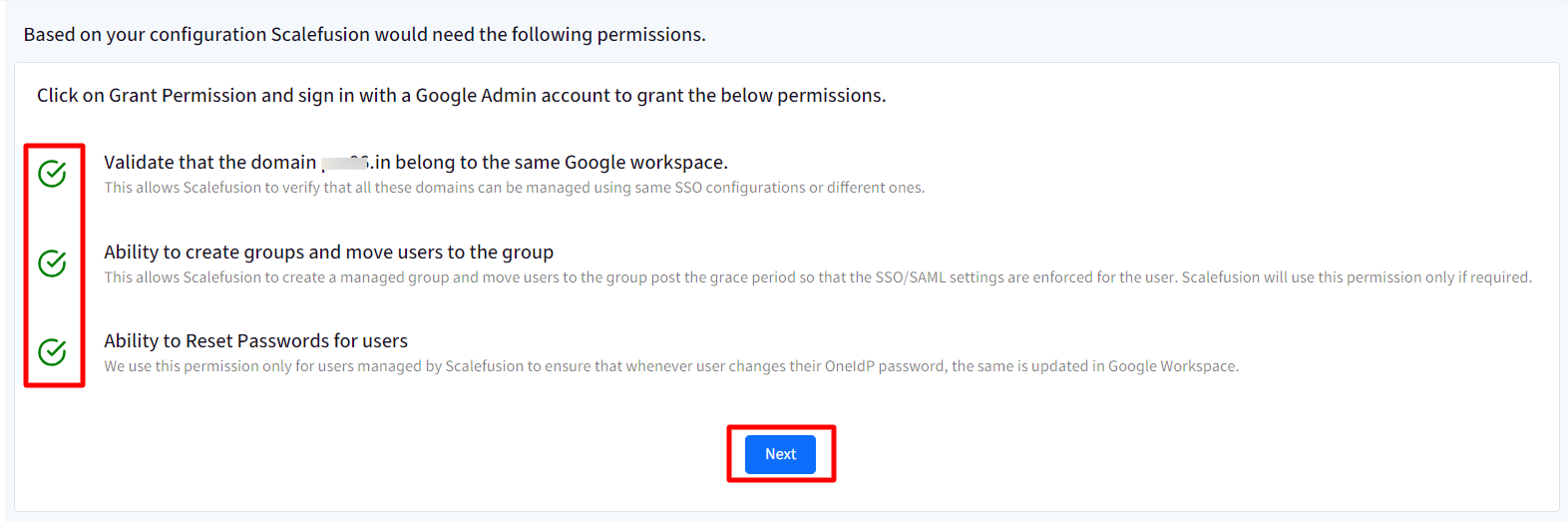
Permissions
Here, you need to grant permissions by signing in with a google admin account:
- Click on Grant Permissions button at the bottom.
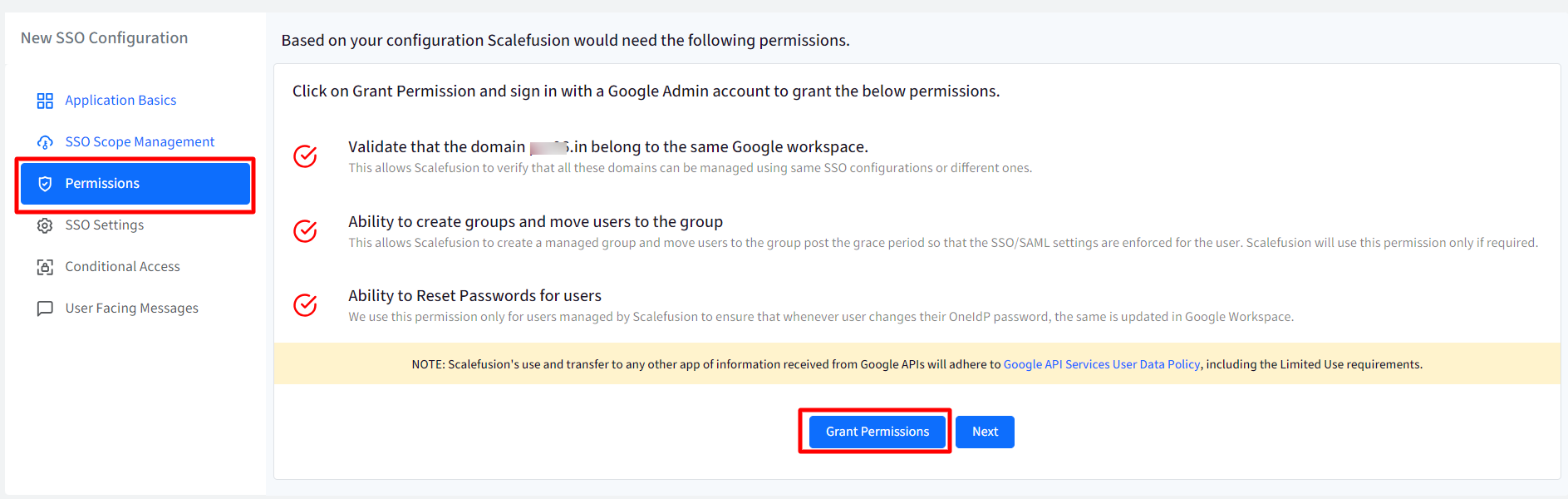
- This will redirect you to google admin account (https://accounts.google.com). Sign in with your google admin account credentials.
- After signing in to google admin, you will be redirected back to Scalefusion Dashboard with permissions granted.
- Note the check mark in front of each permission turns to green color. This indicates that the permissions have been granted.
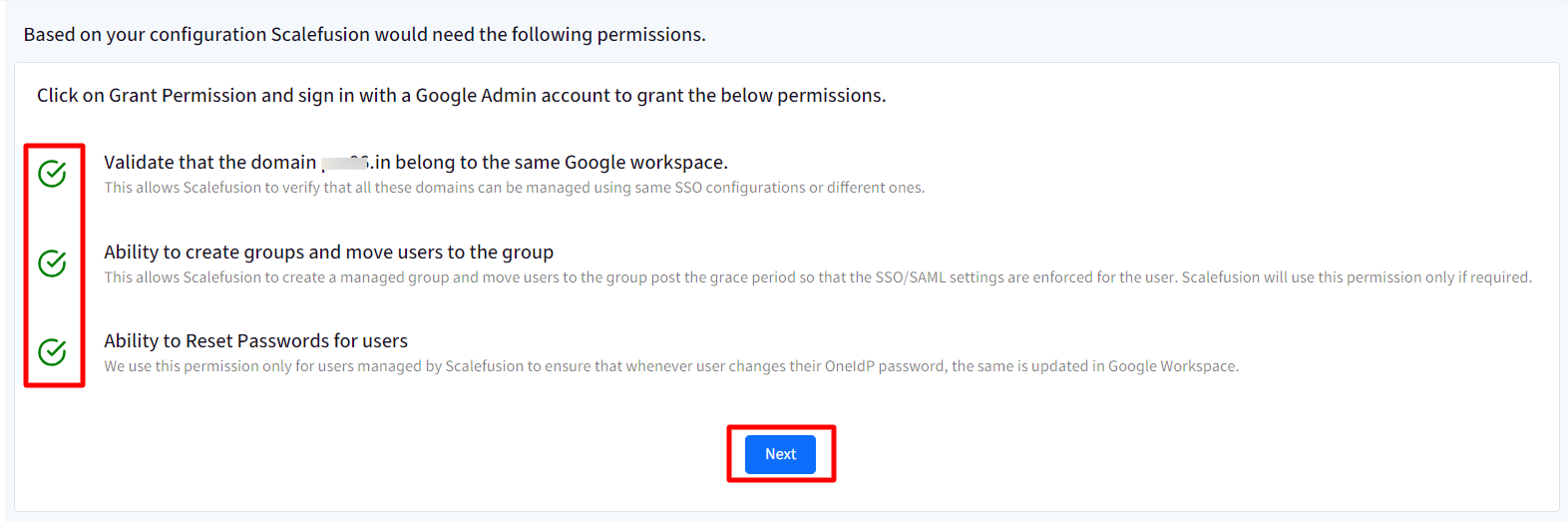
Click Next
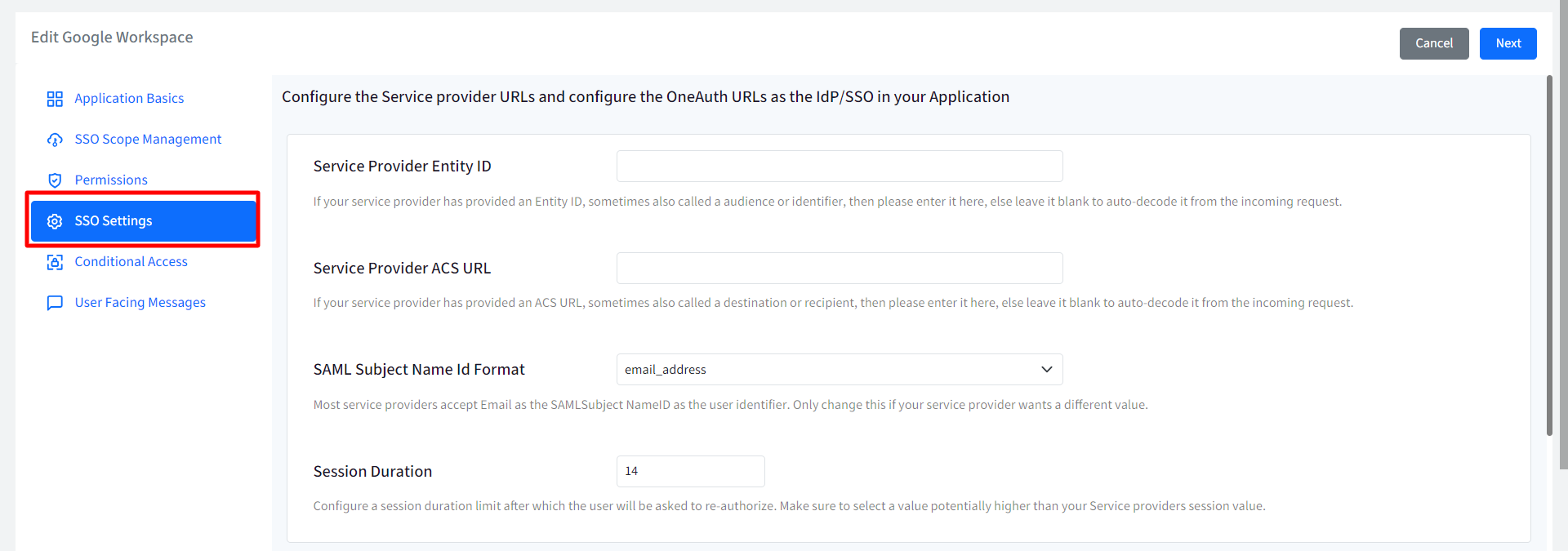
SSO Settings
This section allows admins to configure the Service Provider (Google Workspace) settings and obtain the SSO URLs which will be added to the google admin console.
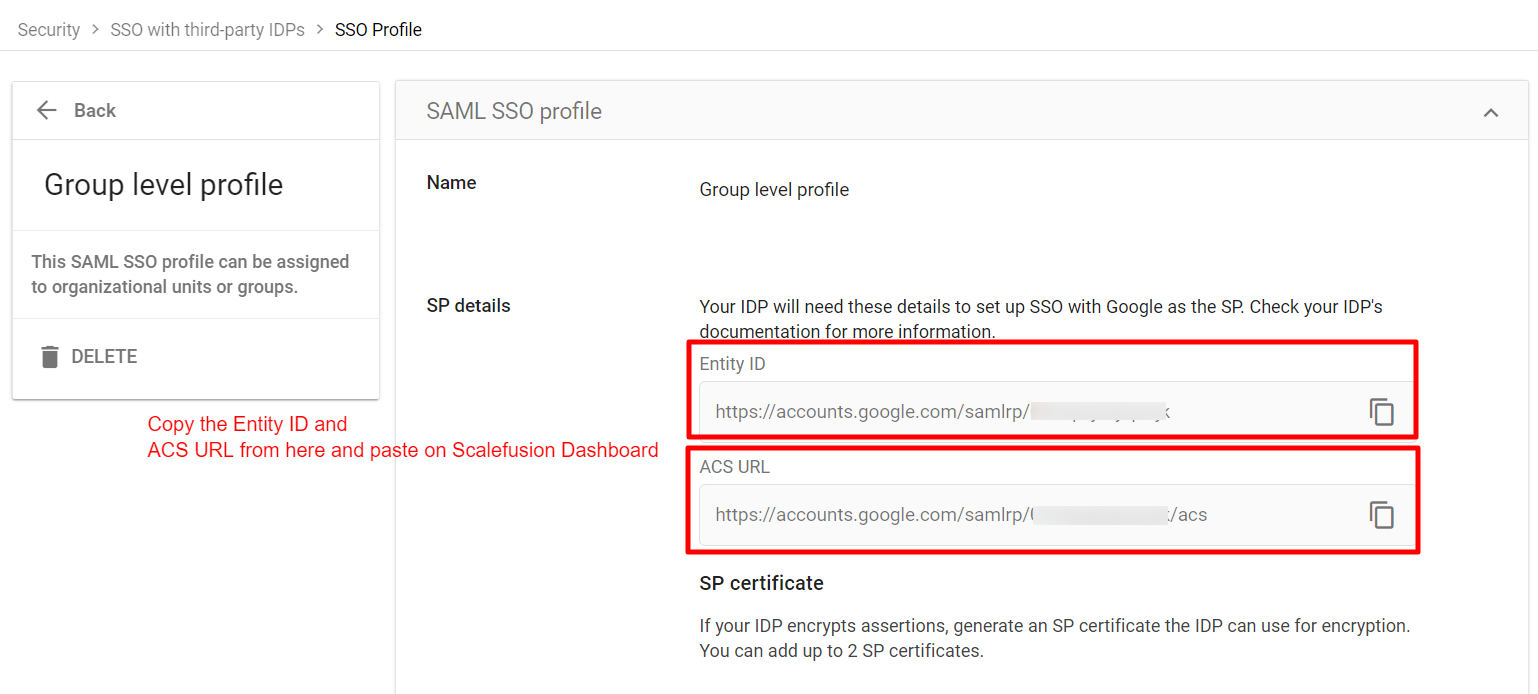
- Enter the Service Provider details on Scalefusion Dashboard, as provided in the web-console of your service provider SSO/SAML section
- Service Provider Entity ID: If your service provider has given you an Entity ID, also known as an audience or identifier, please enter it here. Otherwise, leave it blank to have it automatically decoded from the incoming request.
- Service Provider ACS URL: If your service provider has provided an ACS URL, sometimes also called a destination or recipient, then please enter it here, else leave it blank to auto-decode it from the incoming request
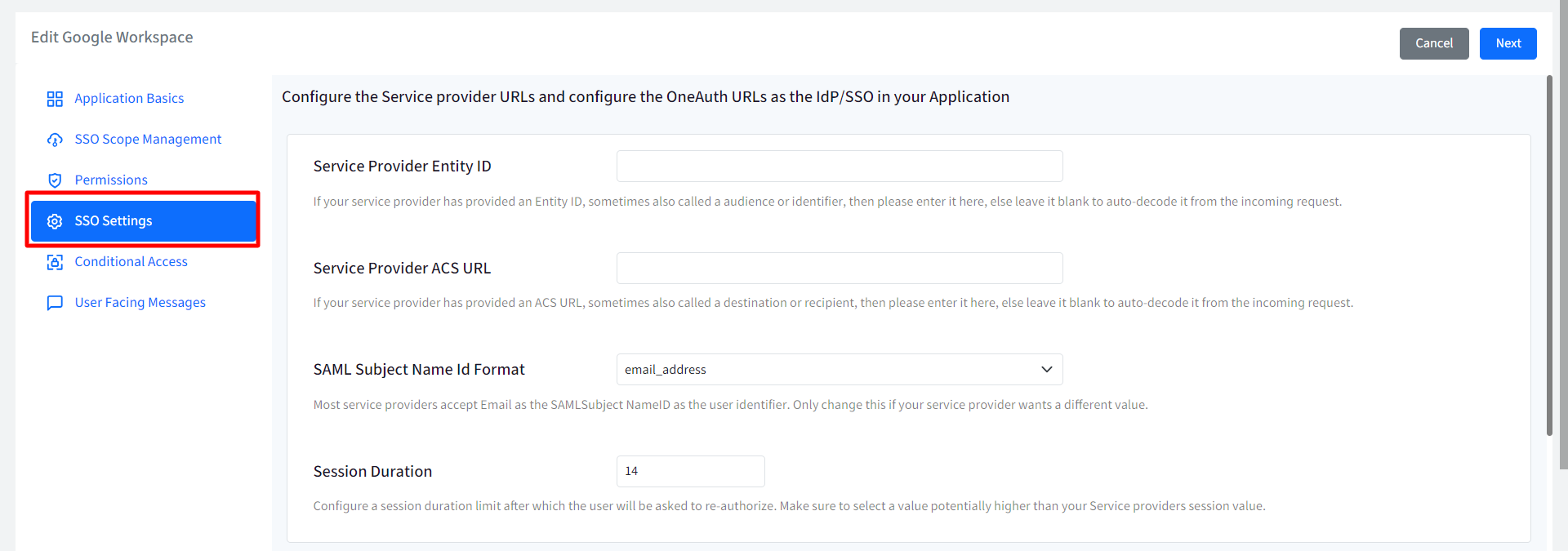
Note: Entity ID and ACS URL is present in the third-party SAML SSO profiles created on google admin console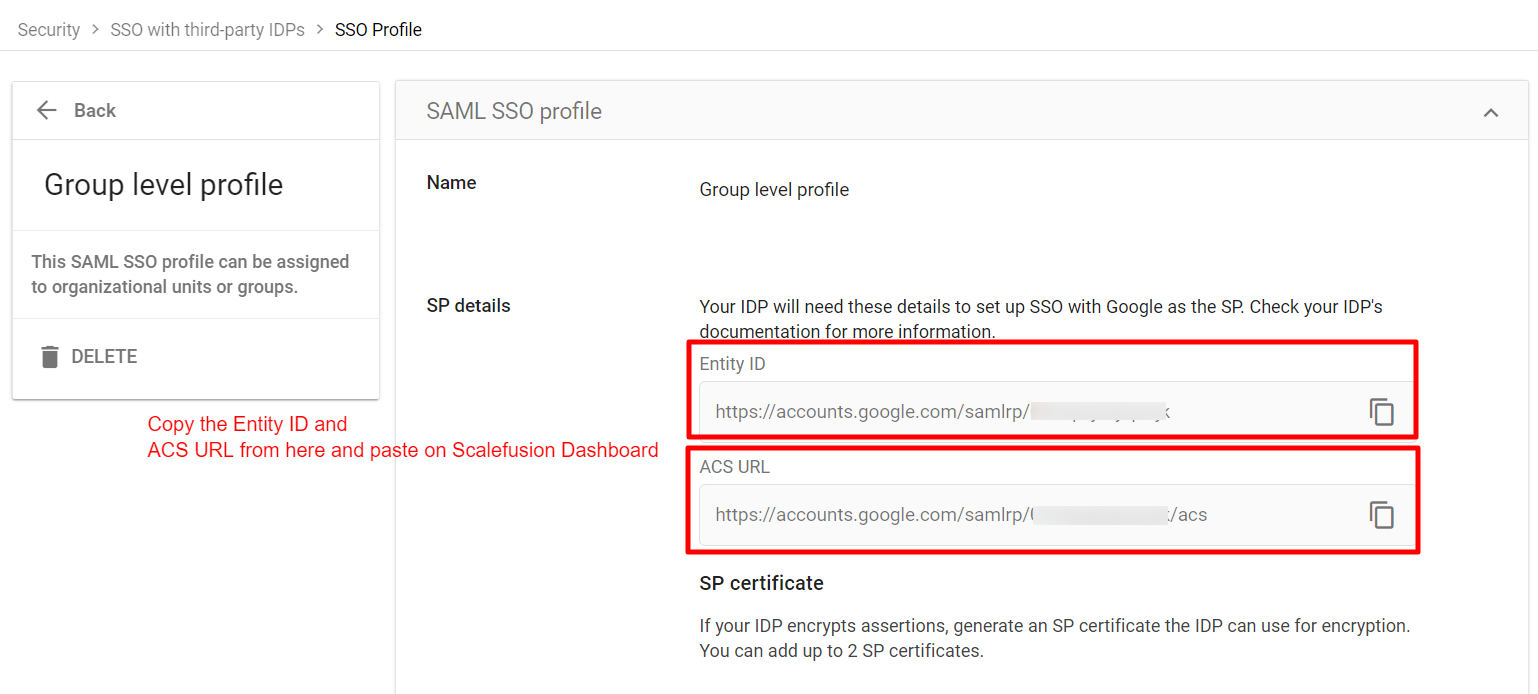
- SAML Subject Name Id Format: Most service providers accept Email as the SAML Subject NameID as the user identifier. Change this only if your service provider wants a different value. Select E-mail or username from the drop-down.
- Session Duration: Configure the duration (in days) after which the user will be asked to re-authorize. Make sure to select a value potentially higher than your Service providers' session value. It can be anywhere from 5 to 90 days.
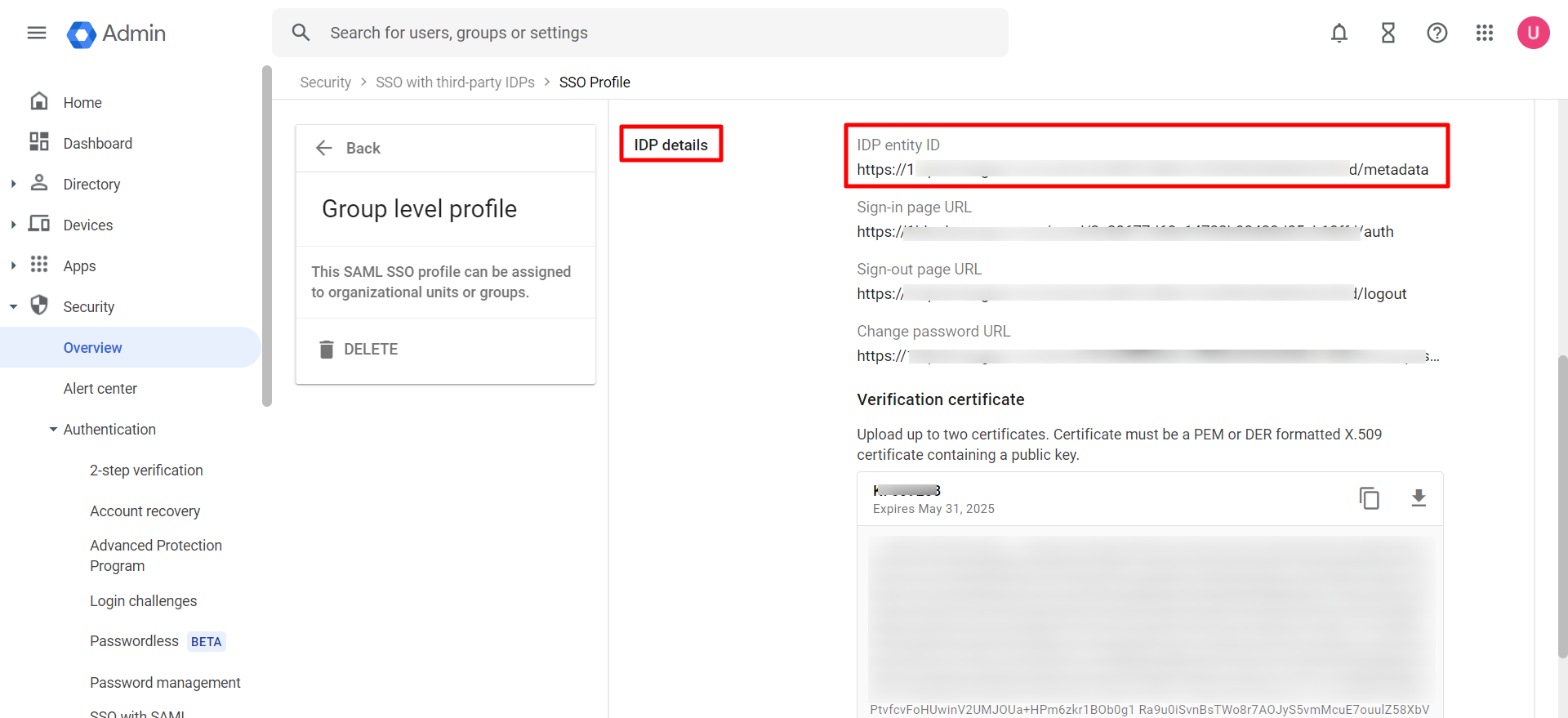
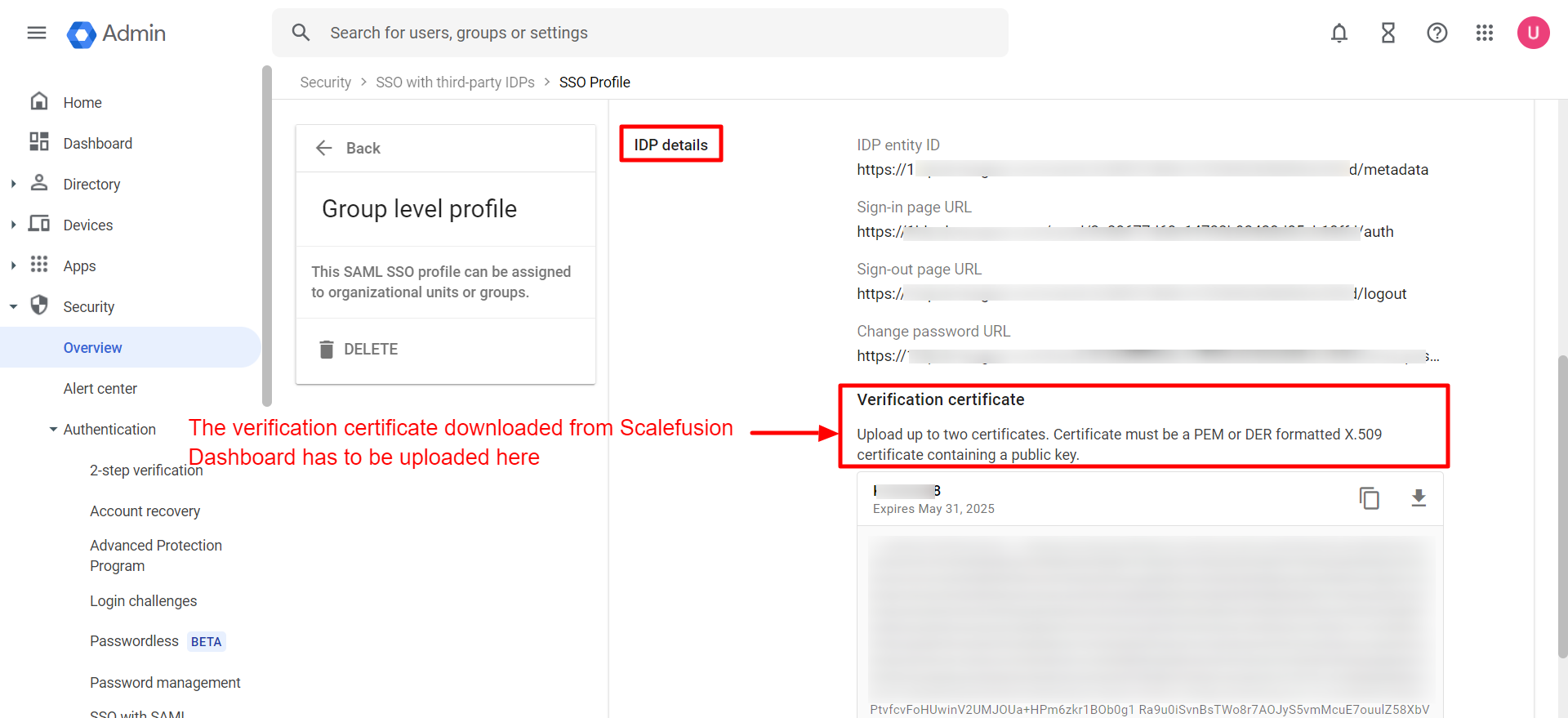
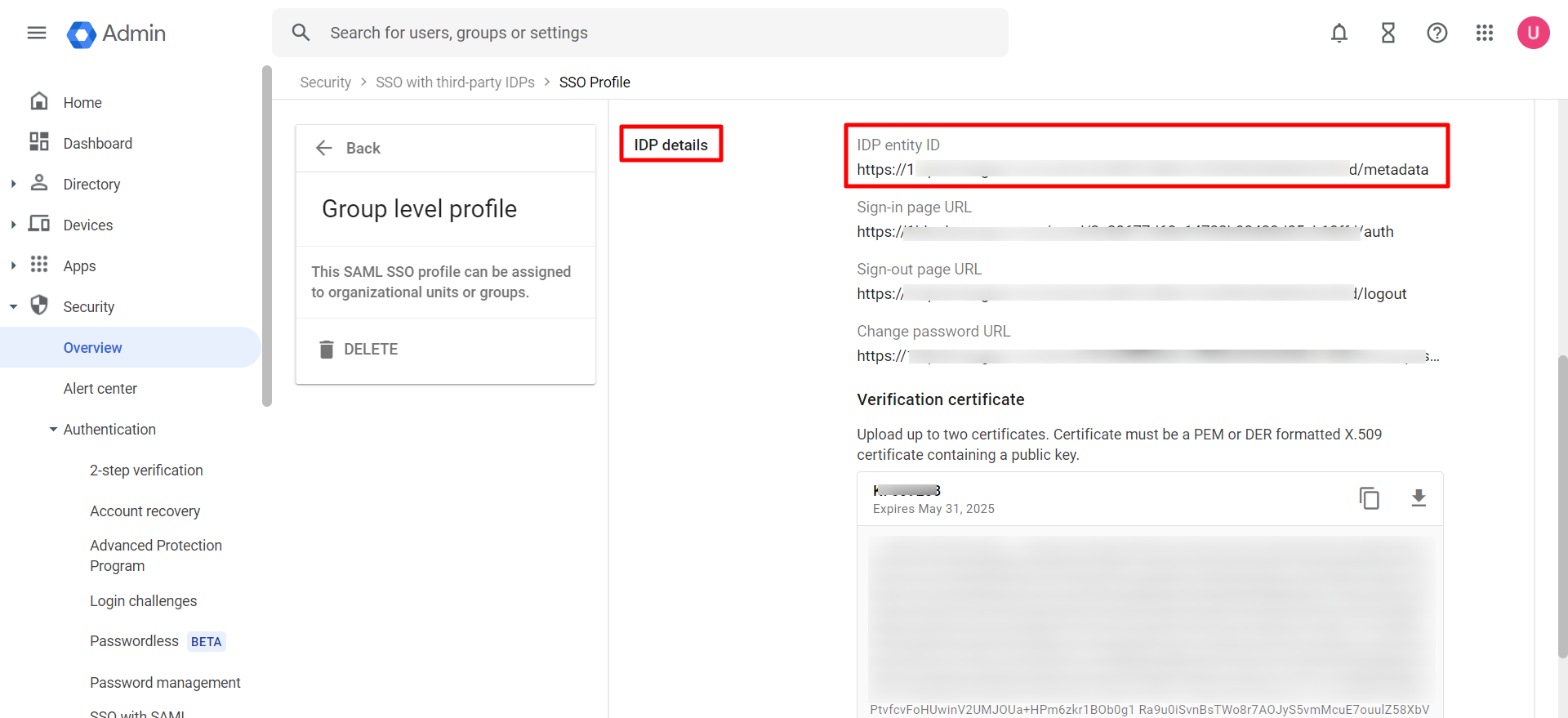
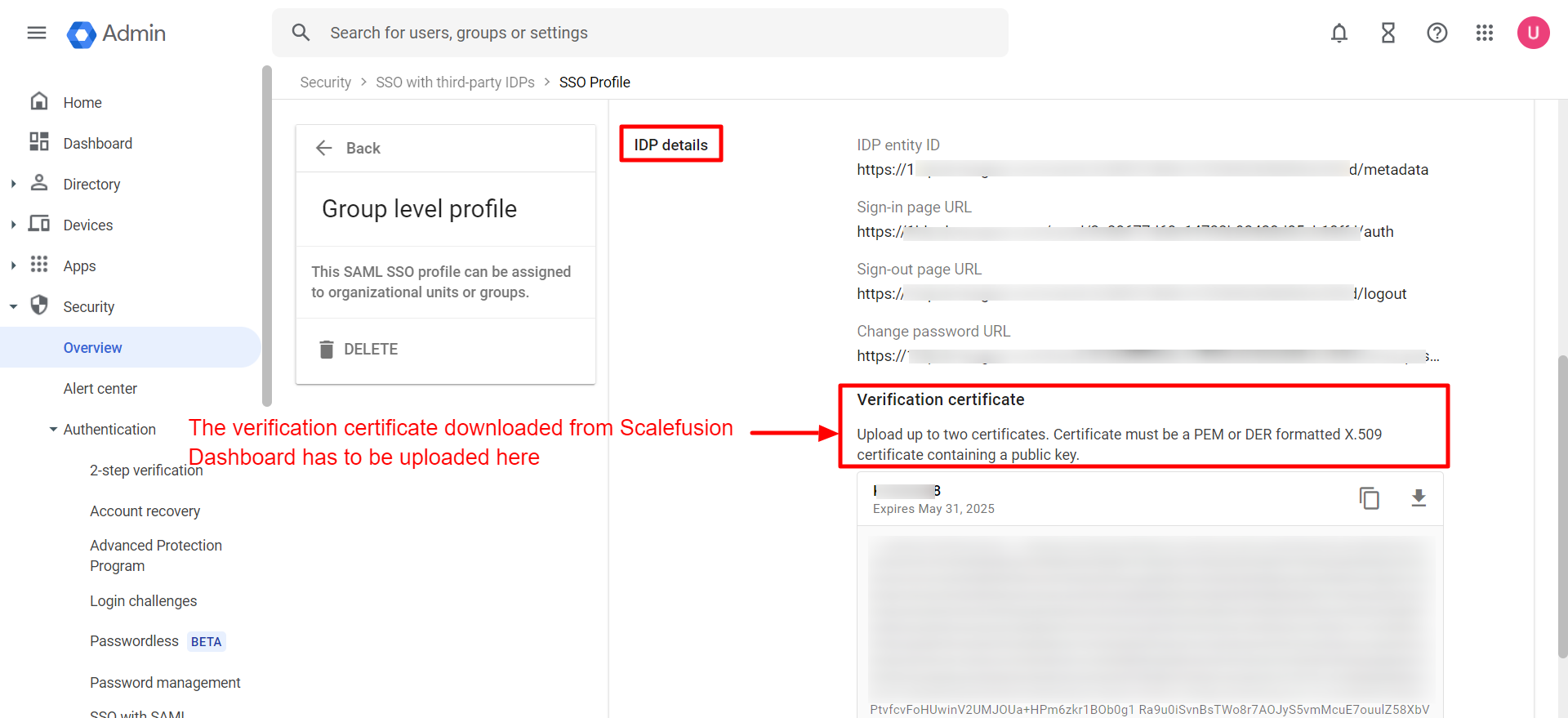
- OneIdP Entity ID: It is the Entity ID of Identity Provider (Scalefusion in this case). Copy this URL from Scalefusion Dashboard and paste it as the Entity ID of the Identity provider on google admin console. To be entered when you add a new SAML profile on the admin console and assign it to groups or organizational units.
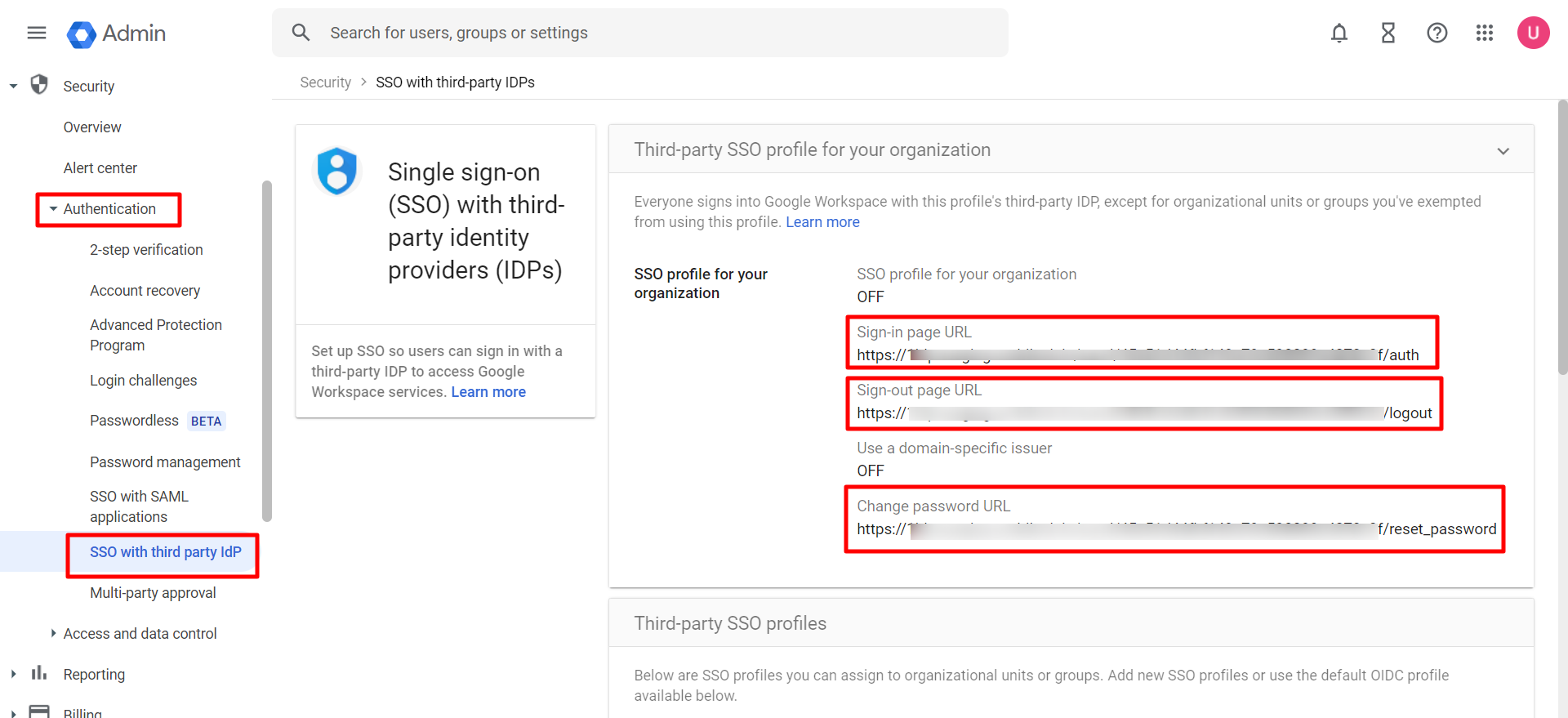
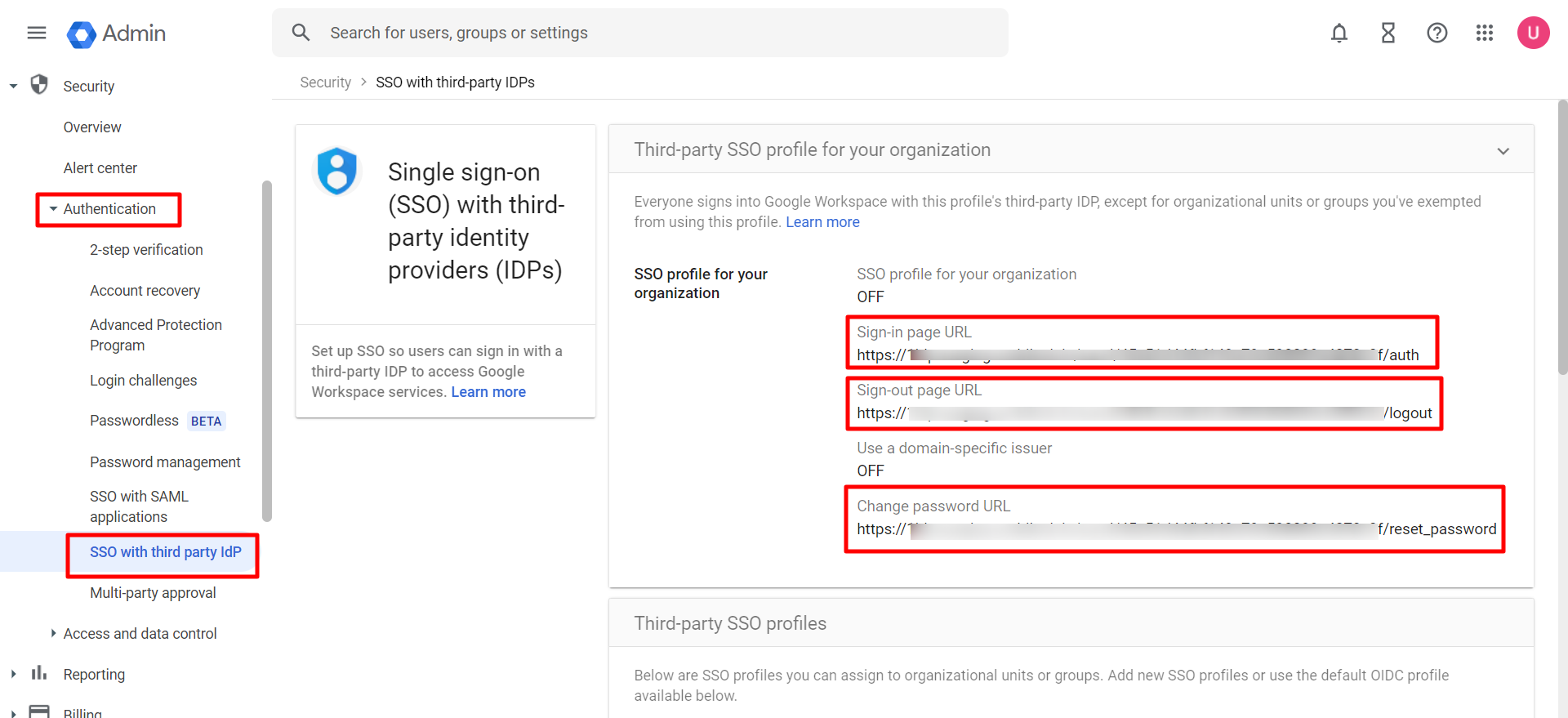
- OneIdP SSO URL: Copy this URL from Scalefusion Dashboard and paste it under the Sign-In page URL on google admin console (Security > Authentication > SSO with third-party identity providers IDPs)
- OneIdP SLO URL: Copy this URL from Scalefusion Dashboard and paste it under the Sign-Out page URL on google admin console (Security > Authentication > SSO with third-party identity providers IDPs)
- OneIdP Change Password URL: Copy this URL from Scalefusion Dashboard and paste it under the Change Password URL on google admin console (Security > Authentication > SSO with third-party identity providers IDPs)
- OneIdP Verification certificate: This certificate is used to sign the response to your service provider (i.e. Google Workspace). Download the certificate by clicking on the download icon on Scalefusion Dashboard. This certificate has to be uploaded at the time of adding a new SAML SSO profile on the admin console.
Click Next
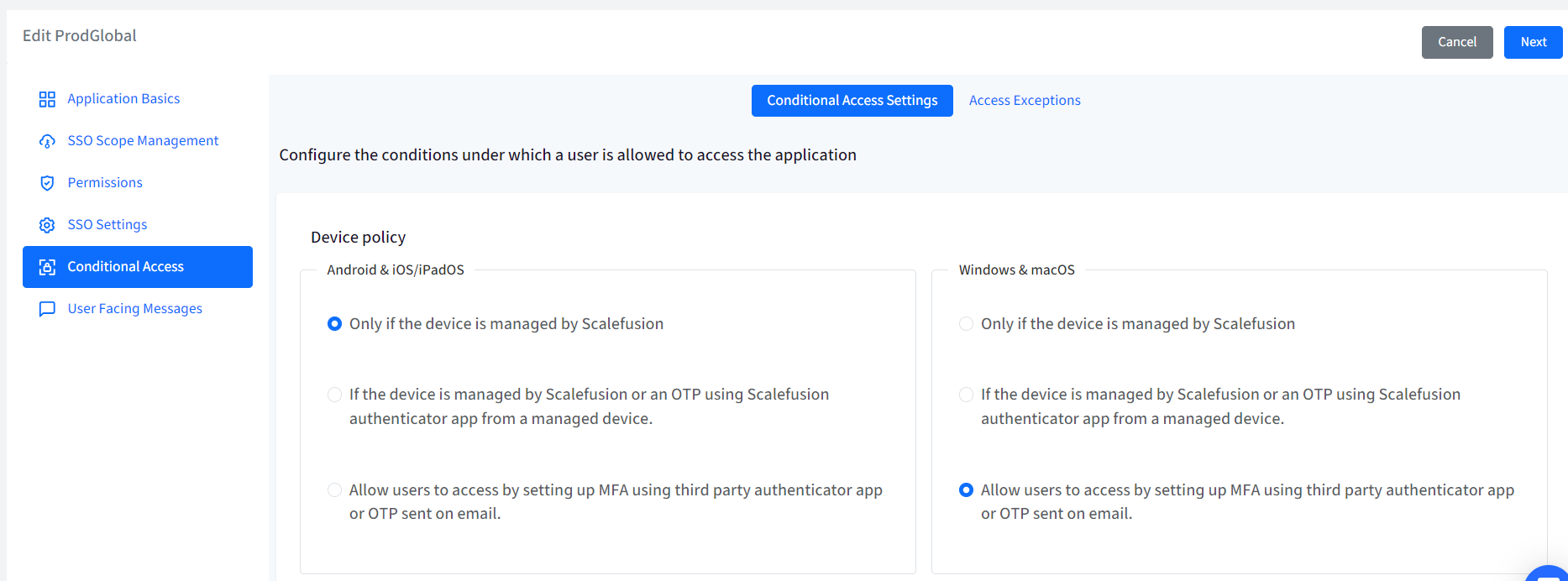
Conditional Access
From this section you can define the additional conditions on the basis of which users will be allowed/disallowed from accessing the application on device. This is divided into following sections:
- Conditional Access Settings
- Access Exceptions
Conditional Access Settings
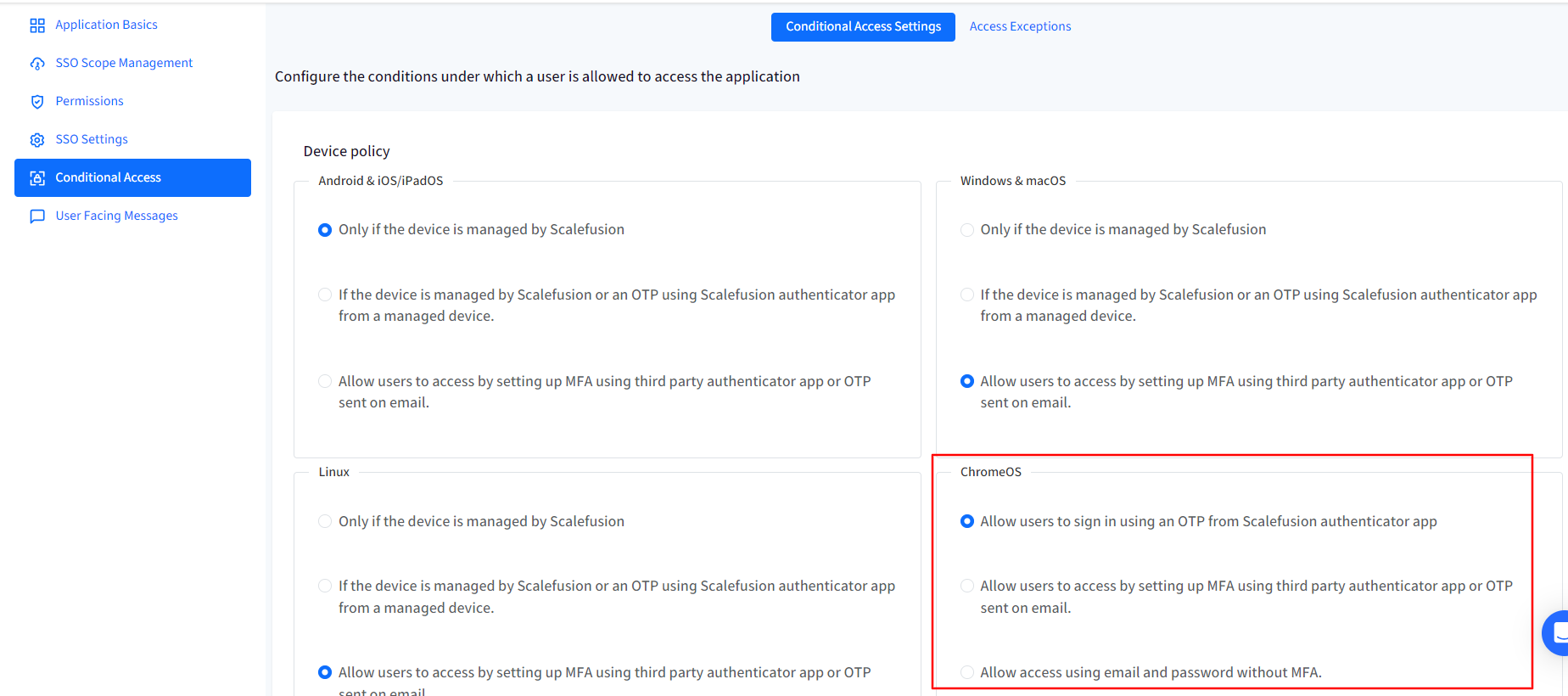
Device Policy
- For Android, iOS/iPad OS, Windows & macOS, Linux: Choose one from the following two conditions:
- Only if the device is managed by Scalefusion: The application will be accessible only on devices managed (enrolled) by Scalefusion
- If the device is managed by Scalefusion or an OTP using Scalefusion Authenticator app from a managed device: The application is accessible if any of the following conditions is met:
- Device is managed by Scalefusion: If device is managed you will not be asked to enter OTP for authentication, or
- If device is unmanaged, OTP is required for authentication. OTP can be taken from Authenticator app installed on a Scalefusion managed device.
- Allow users to access by setting up MFA using third party authenticator app or OTP sent on email:Note:This option will be enabled if MFA is enabled in Directory Settings.
- Device is managed by Scalefusion: If device is managed user will not be asked to enter OTP for authentication.
- If device is unmanaged, OTP is required for authentication. OTP can be taken from any 3rd party authenticator app or an OTP received via email, based on the MFA settings in Directory Settings.
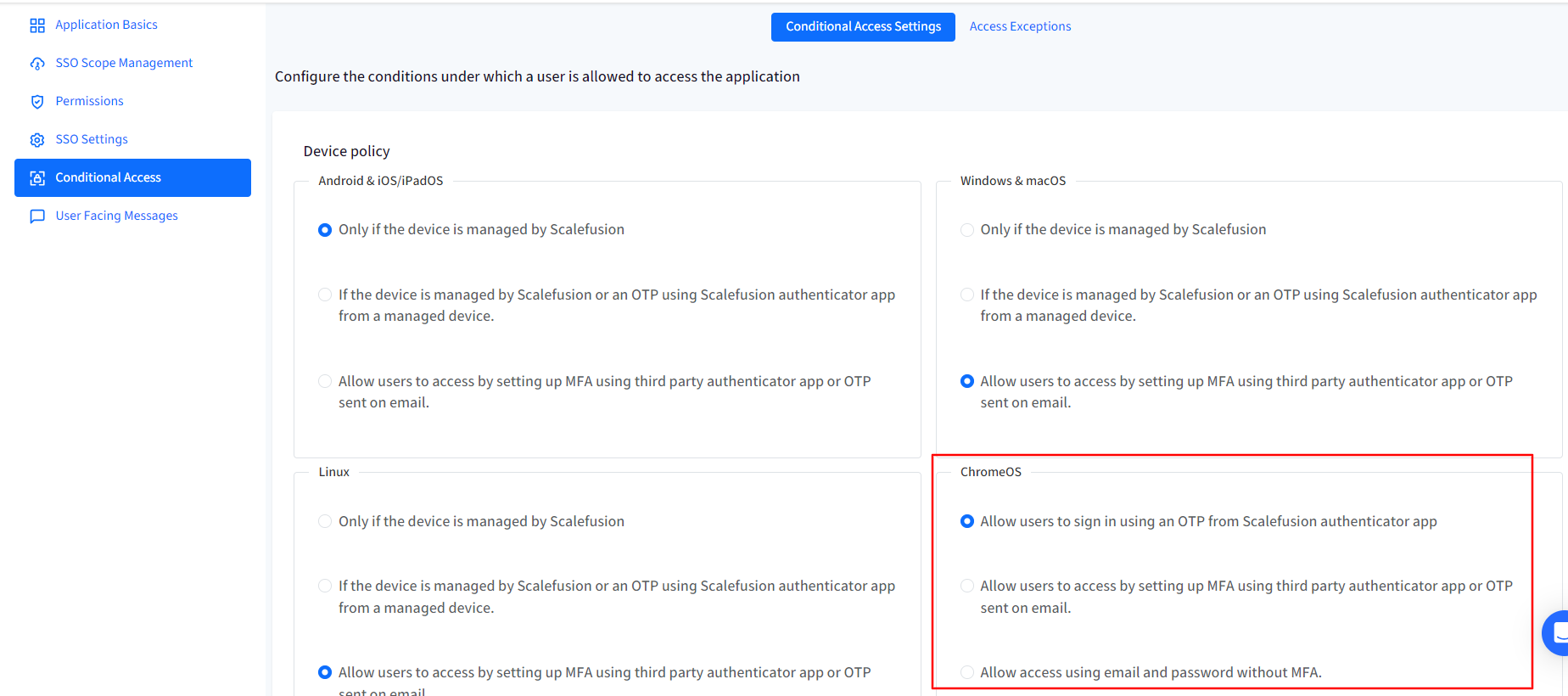
Note: The left side panel is for configuring Device Policy on Android & iOS/iPad OS and right side is for Windows & macOS and Linux below them. Hence, you can configure separate device policies based on platform.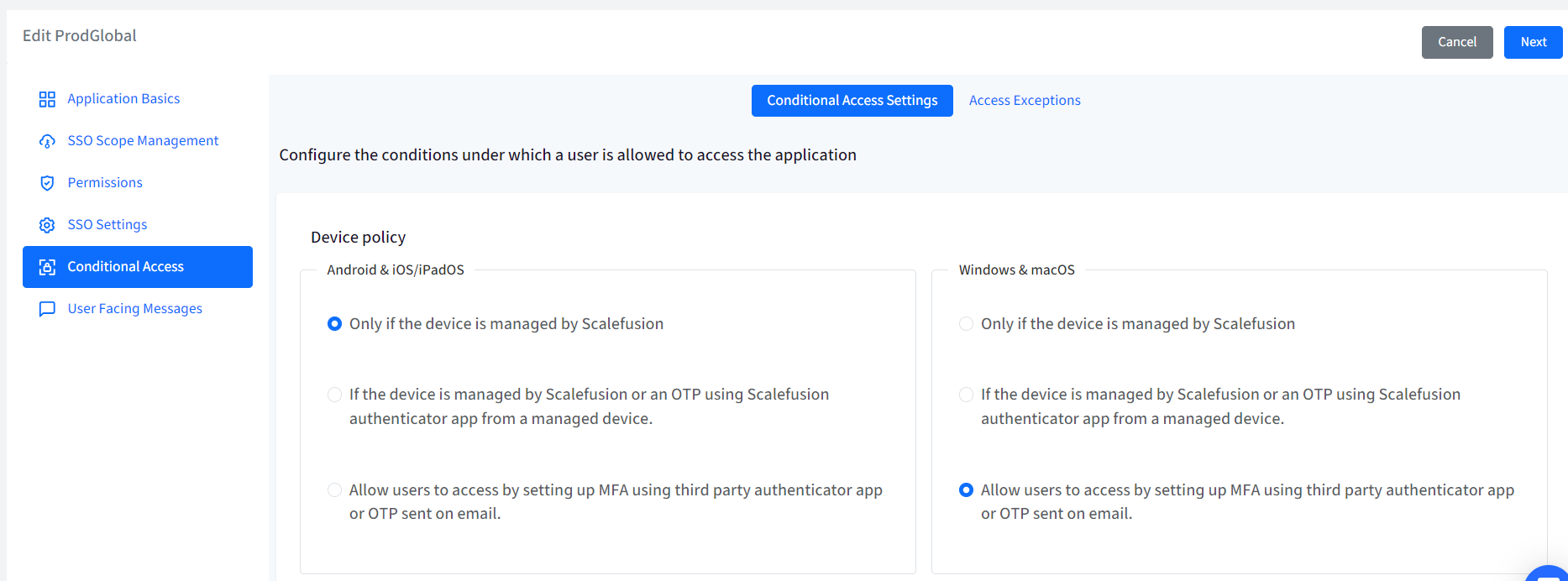
- For ChromeOS:Choose one from the following two conditions:
- Allow users to sign in using an OTP from Scalefusion authenticator app: OTP can be taken from Authenticator app installed on a Scalefusion managed device.
- Allow users to access by setting up MFA using third party authenticator app or OTP sent on email:Note:This option will be enabled if MFA is enabled in Directory Settings.
- OTP is required for authentication. OTP can be taken from any 3rd party authenticator app or an OTP received via email, based on the MFA settings in Directory Settings.
- Allow access using email and password without MFA: Authorization check will not happen, and users can login directly with their email and password.
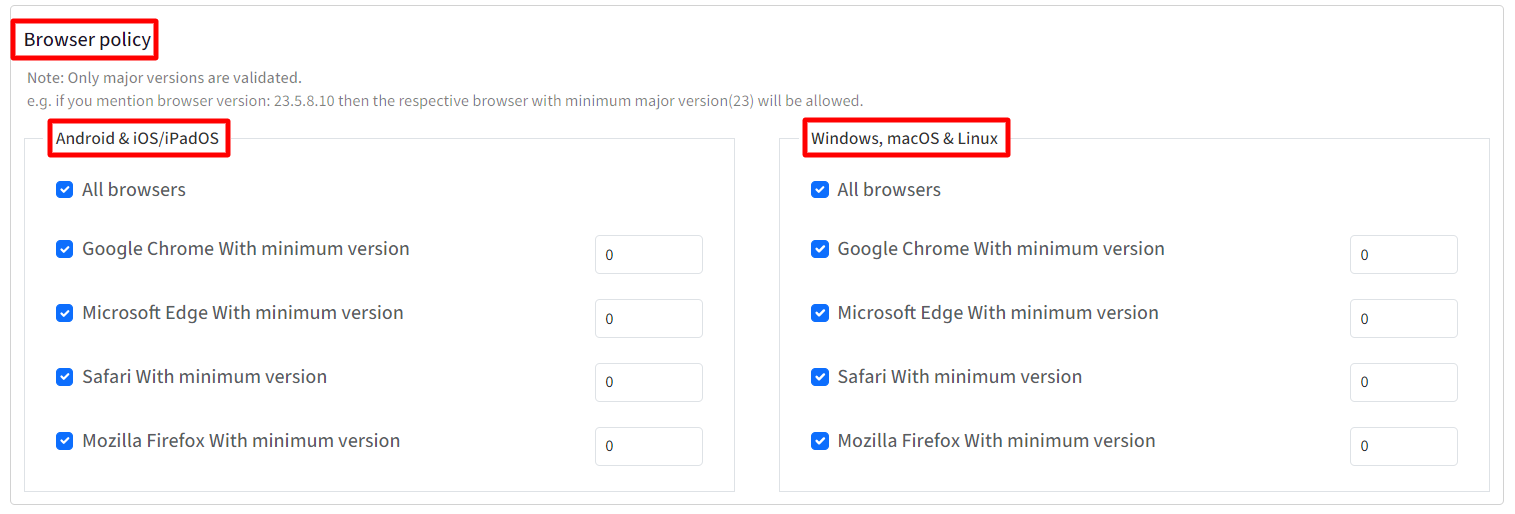
Browser Policy
From here, you can select one or more browsers and specify minimum versions on which you want to allow the access to the application. Following are the options:
- All Browsers
- Google Chrome with minimum version
- Microsoft Edge with minimum version
- Safari with minimum version
- Mozilla Firefox with minimum version
Important Points on Browser Policy:
- By default all browsers are allowed.
- Only major versions are validated. For eg. if you mention browser version: 23.5.8.10 then the respective browser with minimum major version(23) will be allowed.
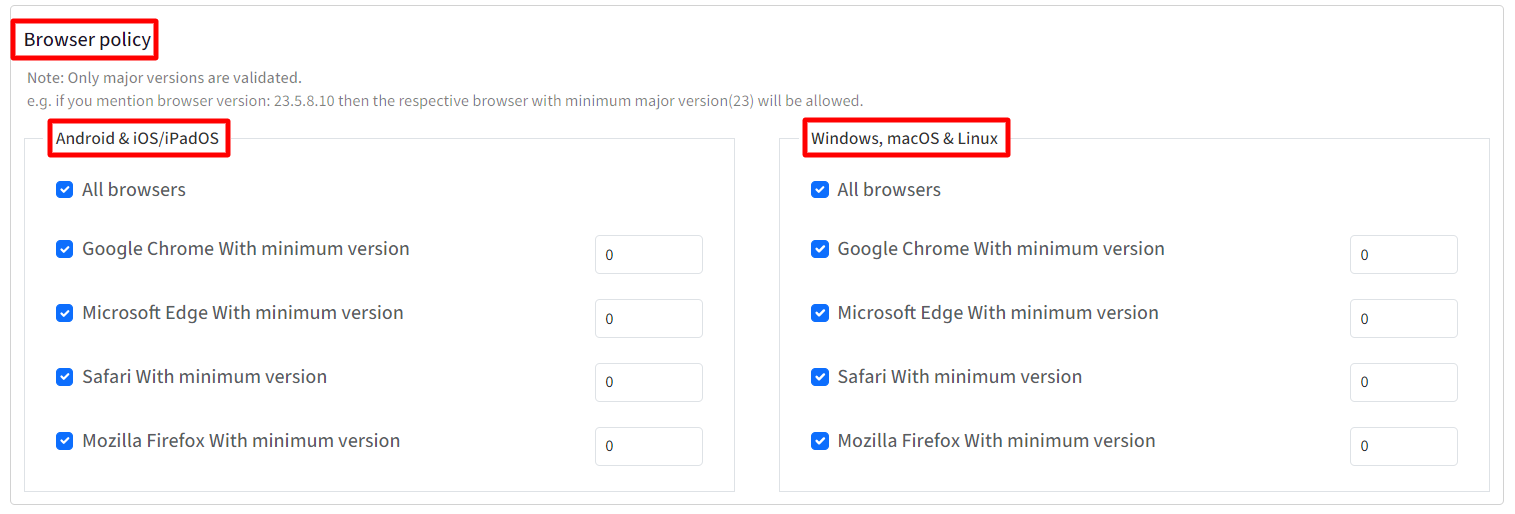
After configuring Device Policy and Browser Policy, click Next
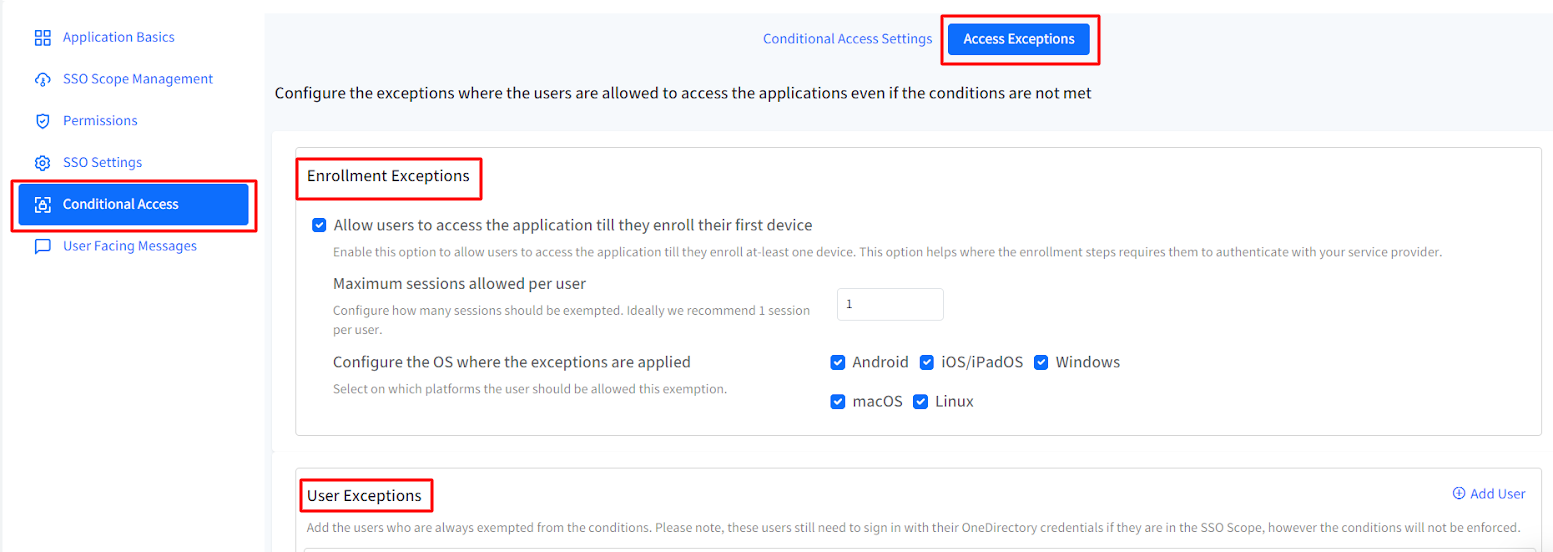
Access Exceptions
From this section you can configure the exceptions where the users are allowed to access the applications even if the conditions are not met. In general, these exceptions will be useful or addresses scenarios where :
- IT Admins have setup Android Enterprise using Google Workspace Or
- IT Admins have setup Apple User Enrollment with ABM/ASM federated to Google Workspace
Following are the exceptions that can be configured:
- Enrollment Exceptions
- Allow users to access the application till they enroll their first device: Allows users to access the application till they enroll at-least one device. This option is helpful in conditions where the enrollment steps requires them to authenticate with the service provider. With this, you can also configure the following:
- Maximum sessions allowed per user: Configure no. of sessions that should be exempted. It can range from 1 to 3. Ideally 1 session per user is recommended.
- Configure the OS where the exceptions are applied: Select the platform(s) on which this exemption would be allowed to users.
- Allow users to access the application till they enroll their first device: Allows users to access the application till they enroll at-least one device. This option is helpful in conditions where the enrollment steps requires them to authenticate with the service provider. With this, you can also configure the following:
- User Exceptions
Here you can add the users who are always exempted from the conditions and will never be asked to manage their device. Enter comma separated email addresses of users or click on Add Users on the right and in the new window, select the users who should be exempted.
Note: These users still need to sign in with their OneDirectory credentials if they fall under the SSO Scope, however the conditions will not be enforced.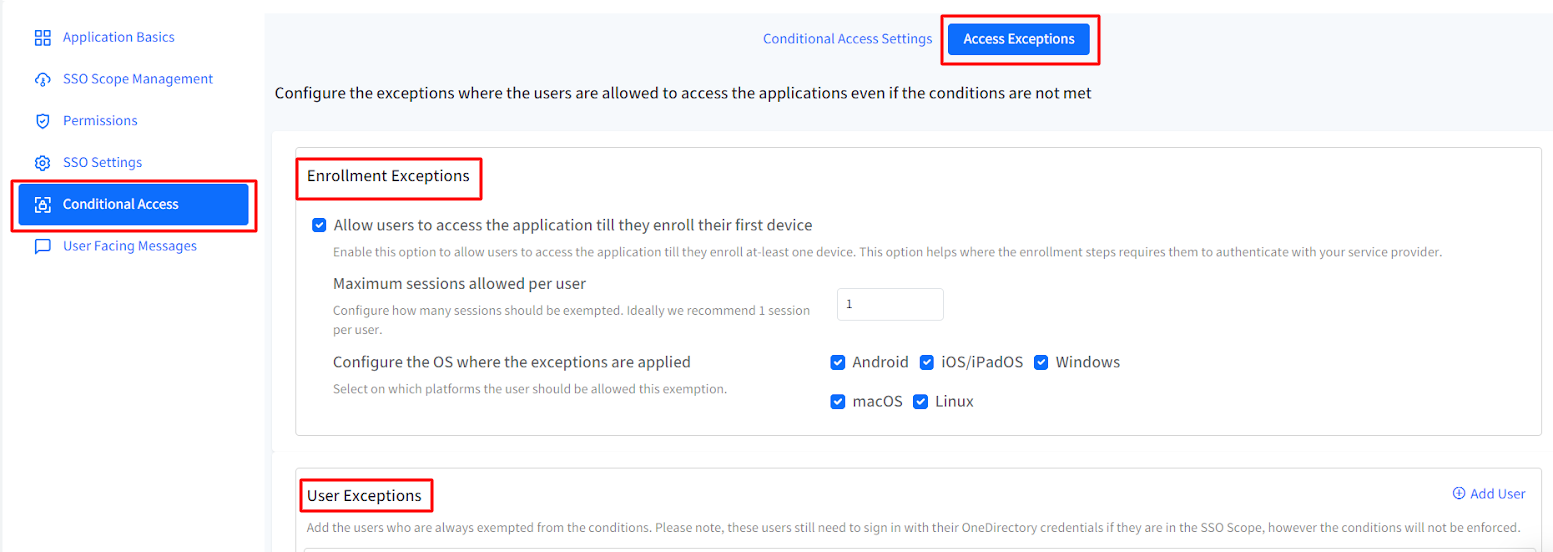
User Facing Messages
User Facing Messages helps admins configure messages that end users may be shown when they are unable to access the application if any of the compliance conditions are not met. You can configure messages under following:
- Configure Instructions for a Non-Compliant Device: This message is shown when the device is not compliant and needs to be enrolled to Scalefusion
- Configure Instructions for a Non-Compliant Browser: Shown when the browser is not compliant as per configurations
- Configure a Message to be displayed when Access is Denied: Any other cases where access to application is denied.
There are some pre-configured messages displayed on Dashboard which you can edit as per requirement.
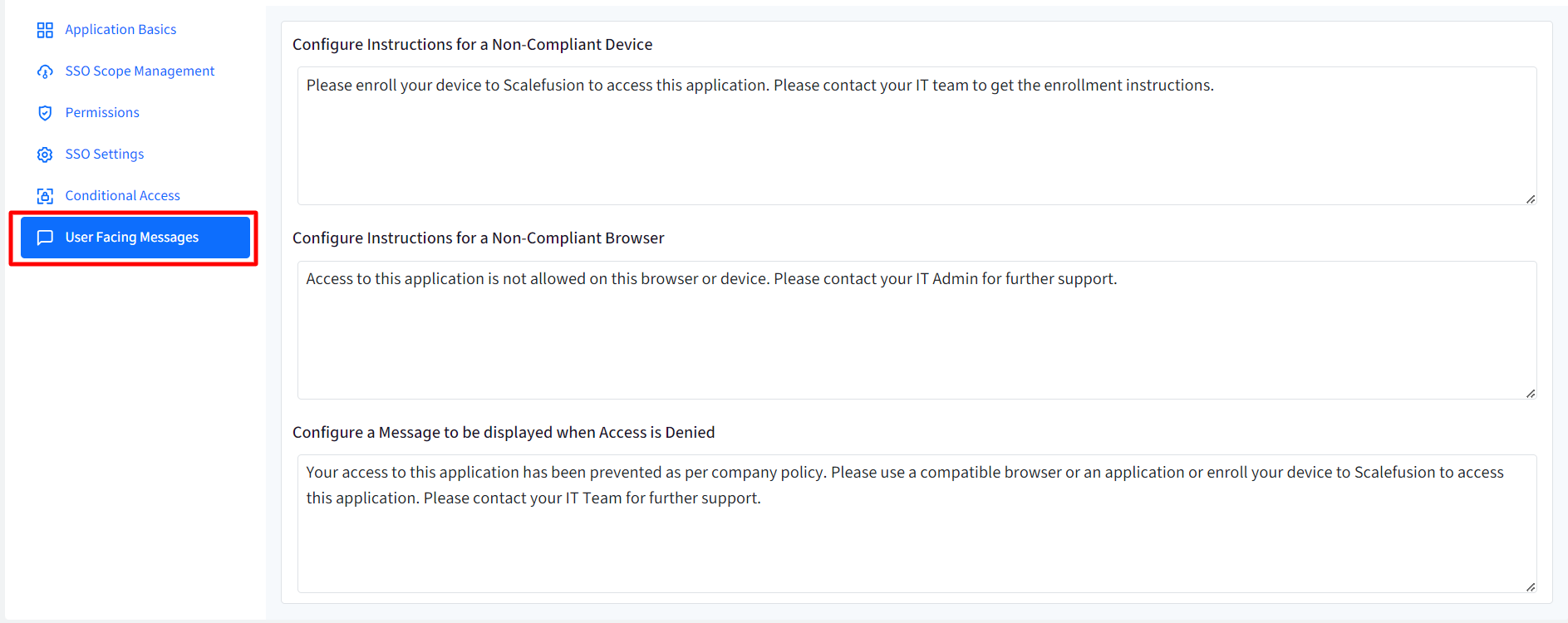
After configuring user facing messages, click on Save
The SSO configuration is created and listed on SSO Configuration page as a separate card with the name you have defined. You can create multiple SSO configurations in the same manner.
The next document explains how the configurations can be managed and other actions you can perform through SSO configurations.